DEEP Conference
We recognized the need to address information security at all levels at the same time and the same place.
We value the importance of knowledge and experience sharing.
Therefore, we provide everyone with the opportunity to share their knowledge and build their new experiences. Dive in and go deep with us.
- Why go deep with us?
- Learn from experts and share your knowledge and ideas
- Share global and local trends
- Network
- Choose topics and tracks by yourself
- Initiate new projects and collaborations
- Who should go deep with us?
- Those who manage corporate and information security
- Folks from the IT and IT security
- Penetration testers
- SOC members from all levels

Drill down to the bit level
Technical and low level stuff is in the focus here. It might be a game for some, but various real-world attack simulations can be expected in here, as well as hacking, exploits and malware dissecting. New ideas on how to identify and exploit vulnerabilities are more than welcome.

Organize your protection!
A combination of technical and management stuff is in the focus here. How to orchestrate people, technology and processes to achieve maximum protection efficiency? Topics such as infrastructure protection, damage control, threat intelligence and incident response. Case studies can be found in this track.

Manage the risks, protect your business!
It’s all about management in here; governance, risk, compliance and business in general. Most of the people in here will try to get everyone on the same high-level page. It’s about understanding each other and dealing with future ideas and collaboration between business areas.
Tuesday, October 20th
- 20:00
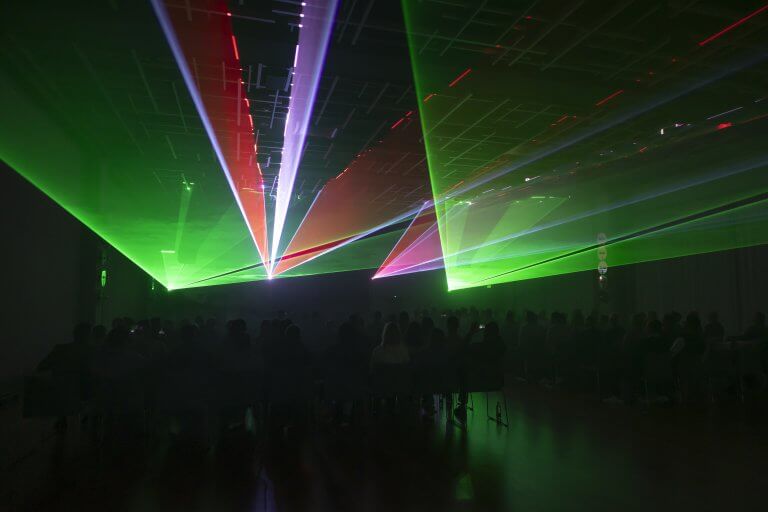
Welcome drink and DEEP quiz
Wednesday, October 21st
- 08:00
Event registration opens - 09:00
Welcome brunch and mingle time - 10:00 - 12:30
Opening ceremony & keynote presentations - 12:30 - 14:00
Lunch break - 14:00 - 18:10
Workshops and presentations
(with a coffee break) - 20:00 - 22:30
Gala dinner - 22:00
DEEP party
Thursday, October 22nd
- 10:00 - 13:30
Workshops and presentations
(with a coffee break) - 13:30 - 15:00
Lunch break - 15:00
Prizes drawing and closing ceremony
Who should go deep with us?
- CEOs, COOs, CTOs and other Cs
- Corporate security managers
- Information security managers
- Chief information security officers
- IT admins
- Members of IT security teams
- Security operation center members
- Penetration testers
- Early Bird Price of one pass for DEEP (21st – 22nd of October 2026. Falkensteiner Hotel & Spa Iadera, Petrčane) is 300 €, VAT included. It is all-inclusive, each conference pass grants you full access to all the areas and contents, presentations, sponsors' booths, workshops, party and meals! Early Bird Price is valid until July 1st, 2026.
- Our aim is to make DEEP an enjoyable experience for all of our attendees, as well as successful one in terms of business. Accommodation is purchased separately and transport to the conference venue isn't included in ticket price.
- Different terms apply for the conference sponsors, so be sure to ask us for detailed info about sponsorship opportunities, you can get them by request, please contact us at [email protected].
Terms And Conditions Uvjeti korištenja
- DEEP will happen in five-star Falkensteiner Hotel & Spa Iadera
- Hotel & Spa Iadera - part of famous Falkensteiner Punta Skala Resort, one of the most beautiful and prestigious tourist complexes in whole Adriatic area.
- Should you have any additional questions please be free to ask us at [email protected]. We are sure that this venue will fully enhance your experience and make your stay there during DEEP more enjoyable.
- Note: If your company/organization’s policy doesn’t support five-star accommodation, please contact us. There is a limited number of four-star rooms available within the Punta Skala resort, at the same price.



at SySS GmbH

at Avola Solutions

at Faculty of Organization and Informatics

at Visage Technologies

Alen Adanić
Software Development Team Lead
at King ICT
Building SSDLC in an Enterprise Environment | .ops
We are currently working on building an SSDLC in organization based on the k8 platform, and we would like to share our experiences in setting it up. We will try to answer the following questions: How do you establish a secure SDLC? How do we comply with various regulatory requirements? What tools should be used for SAST, DAST, SCA, secret scanning, and managing the entire development cycle without compromising delivery speed and quality? Join us for the lecture and hear about our challenges and how we have solved (and are solving) them.
Alen Adanić is the Software Development Team Lead at King ICT, a leading systems integrator in Croatia. With over 10 years of experience in IT, in addition to software development, he focuses on setting up a secure development platform based on the Kubernetes (k8s) platform, incorporating security tools for SAST, DAST, SCA, and ASPM to ensure the same speed of development with a higher level of security and easier compliance with regulatory requirements.

Alen Delić, moderator
CISO
at SpotMe
Roundtable: It's 2025! AI and Cybersecurity are... | .lead
The conversation in this roundtable will focus on the future of Artificial Intelligence and Cybersecurity, as well as the ways in which they will influence each other, intersect, and perhaps potentially even interfere with each other. Through this interesting exchange of thoughts and ideas, the experts gathered here may even come up with the ending of the title for this roundtable. We will find out soon enough.
Moderator:
Alen Delić, CISO @SpotMe
Gosti:
Robert Kopal, Chairman of the Board @EFFECTUS University of Applied Sciences
Marko Horvat, Assistant Professor in Computer Science @FER
Valentina Zadrija, Technical product owner and Senior R&D engineer @Gideon
Hrvoje Kovačević, AI razvoj i infrastruktura @Mindsmiths
Vlatko Košturjak, CTO @Diverto

Alex Ionescu
Technical Director, Platform Operations and Research
at CSE (Communications Security Establishment)
Keynote presentation
Alex Ionescu is the Technical Director, Platform Operations and Research at CSE (Communications Security Establishment), Canada's National Cryptologic Agency. Previously, he was the VP of Endpoint Engineering at CrowdStrike, Inc., where he started as the Founding Chief Architect in 2011. Alex is a world-class security architect and consultant expert in low-level system software, kernel development, security training, and reverse engineering. He is co-author of the last 3 editions of the Windows Internals series. During the last two decades, his work led to the fixing of dozens of critical kernel vulnerabilities in Windows.
Previously, Alex was the lead kernel developer for ReactOS, an open source Windows clone written from scratch, for which he wrote most of the Windows NT-based subsystems. During his studies in Computer Science, Alex worked at Apple on the iOS kernel, boot loader, and drivers on the original core platform team behind the iPhone, iPad, and AppleTV. Alex is also the founder of Winsider Seminars & Solutions Inc., a company that specializes in low-level system software, reverse engineering and security training for various institutions.
Alexander Mitter
| .lead

Alexander Mitter and Paul Sester
CEO / CISO
at KSV1870 Nimbusec GmbH / HORNBACH Group
How HORNBACH, DIY retail group with €6,3 billion in sales, manages 3rd party cyber risk according to NIS2 | .lead
Paul and Alexander will talk you though the process and decisions of a third party cyber risk management program. They will describe why, how and with what help they implemented the program as well as challenges that arose, how they overcame the them and what challenges might still not be answered.
Alexander Mitter is co-founder and CEO of KSV1870 Nimbusec GmbH. Over the last 10 years the company established itself from start-up out of Linz to a major player in the Austrian Cyber Security landscape with a subsidiary in Munich, Germany. In 2019 Alexander initiated the national cooperation leading to the CyberRisk Rating and its ecosystem.
Paul Sester is the CISO of the HORNBACH Group. For 9 years now Paul works for HORNBACH and for 5 years he is responsible for information security.

Ana Balaško
Telecommunications manager
at HEP ODS
Building Secure Process Environments: The Role of IEC 62443 in Process Systems | .lead
Owners of process systems are facing increasing risks due to the convergence of operational technology (OT) and information technology (IT). The IEC 62443 standard provides comprehensive guidelines for the design, implementation, and maintenance of security mechanisms to protect OT systems from cyber threats. This presentation will outline why it is crucial for process system owners to understand and implement IEC 62443 as a specific tool to enhance security, alongside the complementary application of ISO 27001 and the NIS Directive, in order to ensure holistic protection of critical control systems.
Ana Balaško graduated in 2009 with a degree in Electrical Engineering from the Faculty of Electrical Engineering and Computing in Zagreb, where she is also completeing postgraduate specialist studies in Information Security. She has been employed at HEP ODS since 2010, where she actively participates in the company’s strategy development in the fields of process systems, telecommunications technologies, and cybersecurity, as well as in managing projects aimed at achieving business objectives within her area of expertise. Ana has been involved in several innovative projects focused on the use of advanced technologies in industrial environments and creating the prerequisites for transforming the distribution system into an environment capable of handling the main challenges of distribution flexibility in a cyber-secure manner. She is an active participant in conferences such as CIRED, MIPRO, and others.

Andras Herceg and Tihomir Maček
Senior System Engineer / Sr. Product Manager for Cyber Security
at Rubrik / Ingram Micro
Your Backup is Lying to You. (Here's Why.) | .tech
Every traditional backup solution introduces hidden risk—the risk of non-recoverable data, a security attack surface, and slow, uncertain recovery. Attend this technical deep-dive to see the definitive proof of these flaws and learn how Zero Trust Data Security fundamentally changes the recovery game. We’ll show you how a natively cyber-resistant platform pioneers data security, enabling you to perform surgical threat hunting within your backups. Discover the solution that helps companies avoid massive revenue loss and ensures long-term business continuity—even after a full-scale cyber-attack.
Andras is a seasoned professional with over 17 years of experience in enterprise software-defined data center infrastructure. He has a deep background in architecture, automation, security, and consulting, gained from working on the customer side, system integrator side (NTT), and on vendor side (VMware).
Since December 2022, he has been a Senior System Engineer at Rubrik, covering the South Eastern Europe and Levant regions. A lifelong learner, Andras holds over 50 IT and VMware certifications, including VCIX-DCV, VCIX-CMA, and five VCAPs.
Outside of work, Andras is passionate about Home Assistant and automation, enjoys road cycling, running and paragliding, and is a proud father of two.
Tihomir Maček is an experienced Sales Professional specializing in Cyber Security within the fast-paced IT distribution industry. Throughout his career, he has worked closely with leading global vendors, supporting partners and clients in strengthening their cyber resilience and achieving business success. His professional journey reflects a strong dedication to building trusted relationships, delivering value-driven solutions, and staying ahead in the ever-evolving cybersecurity landscape. Beyond his professional life, Tihomir enjoys skiing, spearfishing, and travelling in his free time.

Andrej Andelic and Andras Herceg
Account Executive / Senior System Engineer
at Rubrik
Reducing the (Financial) Impact of successful Cyber-Attacks | .lead
Cyber resilience is business resilience! Analysts assume that in 10 years, we will experience a successful ransomware attack approximately every 2 seconds. So it's not a question of whether you will be attacked, nor when, but how often. In this presentation, you will learn why Backup is not the same as Cyber Recovery and how you can proactively reduce the attack surface in the long term in order to reduce or even completely compensate for the possible damage. You will also learn how to generate cyber intelligence from backup data in order to react in a targeted and NIS2-compliant manner. Keep in mind legacy RTO agreements do not meet today's required Cyber-RTO's!
Andrej Andelic is Account Executive for South Eastern Europe at Rubrik. Andrej has been working as an engineer in the telecom industry until 2012 and since then had different presales and sales roles in ICT industry within number of multinational companies such as Microsoft, Infobip, Deutsche Telekom Croatia, Nexi Group. In Rubrik, he's account executive responsible for customer relationships in SEE region.
Andras Herceg is Senior System Engineer for Middle Europe and the Adriatic at Rubrik. Andras has 16 years of professional experience in enterprise software-defined data center infrastructure architecture, automation, security and consulting - at the Customer, system integrator (NTT) and Vendor (VMware) side. Currently, at Rubrik he is covering Middle Europe and Adriatic as a Senior System Engineer, since December 2022. Lifelong learner, accomplished 50+ IT and VMware certifications, including VCIX-DCV & VCIX-CMA, 5x VCAPs. Home Assistant and automation geek, road cycling, paraglider and father of two little hackers.

Antoine d’Haussy
OT Security Practice Head EMEA
at Fortinet
Securing the IT/OT convergence at Critical Infrastructures | .ops
With Critical Infrastructures becoming more interconnected, securing the OT side is more vital than ever. This presentation will examine the unique cybersecurity challenges OT environments face and how their convergence with IT, Cloud, and wireless technologies including 5G exposes new vulnerabilities. We will explore best practices, such as network segmentation, secure remote access, and monitoring for industrial control systems (ICS), while referencing standards like IEC 62443.
Using real-world examples, we will also show how solutions like Fortinet's security fabric help mitigate risks without disrupting operations, offering actionable insights to strengthen the resilience of critical infrastructure and comply to IT/OT security frameworks.
Antoine joined Fortinet in 2019 to lead the OT strategy and revenue growth in EMEA. With 25 years’ experience in product management, engineering, sales and marketing, Antoine mostly worked for industrial clients together with Fortinet, General Electric, ALSTOM, and Altran.
In his product management roles for Control vendors, he was leading the digital solution portfolio including the M&D as well as Cyber Security products and services solutions.
Antoine participated to several global events as a speaker and panelist. He is contributor into industrial cybersecurity working group, he is a certified Global Industrial Cyber Professional (GIAC-GICSP) trained at SANS institute, he holds a MSc of Radiocom, Networking & IT and an MBA.
A native of Paris, he lived in several countries to finally settle in Zurich area in Switzerland, where he enjoys spending quality time with his wife and two kids.

Bojan Belušić
Head of InfoSec and IT Ops
at Microblink
Cyber Resilience Act & Security by Design | .ops
EU's Cyber Resilience Act (CRA) is one of the most anticipated acts in the Dev community, and yet one of the least talked-about on a general scale. It will probably be the first regulation of its kind in the world and it will affect most of the digital and software products sold in the EU. The CRA will require that products are released to the market with all known vulnerabilities addressed and developed by following secure by design principles, starting with a cybersecurity risk assessment of a product. This presentation will try to sum up what all this could mean for a software development company working on products included in the scope of the CRA.
Bojan Belušić is the Head of InfoSec and IT Ops in Microblink, one of the leading companies in AI and software development in Croatia. After 10+ years of experience in the financial industry as a sysadmin, IT architect, and IT auditor, he is now driving security and IT operations in a fast-paced development environment, balancing developers needs and compliance, while keeping those development environments secure.
Bojan Magušić
| .ops

Bojan Magušić
Product Manager on the Customer Experience Engineering Team
at Microsoft
Cloud Infrastructure Security | .ops
Presentation outline: What I want to share with you in this session is important and it affects companies big and small. I'd like to start with an example of a real world breach (without mentioning any names). I'll walk you through what happened, covering the impact to the company itself, followed by what could have been done to prevent it. Here I'll touch on the importance of ensuring that cloud resources adhere to best practice guidance and share with you some trends I see in the real world. Some misconfigurations tend to be more riskier than others, for example open ports carry more risk to your organization's overall security posture than enabling logging. I'll also share with you what cloud services I typically see targeted the most. Even for organizations that use more than one public cloud provider. While detecting misconfigurations in your cloud environments is important, ideally after you remediate misconfigurations, this should be applied to how you deploy resources going forward. Ensuring misconfigurations that you detected, don't happen again going forward. Here I'll speak about the importance of applying best practice guidance at scale, ensuring consistency across your environment and even integrating with pre-deployment (keyword: SecDevOps). While the industry is full of jargon of tools that can be used by different vendors to help with the technology side of things, interestingly enough implementing sound security hygiene continues to be the least attractive yet highly effective practice that companies can do to minimize the likelihood of security incidents. One might ask themselves, what is then the problem with efficiently implementing sound security hygiene in the real world? I'd like to offer a perspective. It's not just having the right tools in place, it has very much to do with the way that people operate them and how they're used inside of an organization. This is why as part of this session, I'll share with you some best practices I've seen in the real world on how organizations approach governance, readiness and leadership sponsorship.
Free takeaways:
At the end of this session, you can expect to:
- Be able to explain why security hygiene should be an organizational-wide priority
- Understand how lack of security hygiene can impact your organization and its business
- Understand which security misconfigurations of cloud services you should prioritize and fix first
- Understand which cloud services are targeted more often than others, even across multicloud
- How to use Infrastructure as Code to embed security hygiene into pre-deployment
- Learn how to integrate continuous monitoring of cloud workloads with CI/CD and IaC
- Learn how other organizations are approaching governance and leadership sponsorship
Bojan is technologist, published author, and public speaker on cybersecurity topics.
Working with Microsoft as a Product Manager on the Customer Experience Engineering Team, where I act as a technology expert for Fortune 500 companies on the most complex and leading edge deployments, that help them realize the full value of their security investments and improve their overall security posture.
Author of the Manning book on Azure Security, a practical guide to the native security services of Microsoft Azure that teaches how to use native security services of Azure to effectively improve system security and secure the various resources in the environment against threats.
I have a strong passion for cybersecurity, advancing women in tech and professional development. I'm very interested in building partnerships with other companies and cyber professionals to learn how they support, advance, and retain their cyber talent.
In addition to various technical certifications (21+ and counting), I've also received certifications from INSEAD and Kellogg School of Management.

Bojan Magušić
Senior product Manager on the Customer Experience Engineering Team
at Microsoft
Securing AI in the Wild: Protecting Your GenAI Applications from Emerging Threats | .lead
Have you ever wondered how organizations secure their AI applications in the real world? With the rise of tools like ChatGPT, more companies are building their own generative AI (GenAI) applications—but securing these apps is no easy task. The uniqueness of GenAI introduces a new and complex attack surface. In this session, I’ll dive into how real-world companies are tackling security challenges for their GenAI apps. From new attack vectors like prompt injection to other emerging threats, we’ll explore the strategies organizations are using to protect their AI-driven innovations.
Bojan is technologist, published author, and public speaker on cybersecurity topics.
Working with Microsoft as a Senior Product Manager on the Customer Experience Engineering Team, where I act as a technology expert for Fortune 500 companies on the most complex and leading edge deployments, that help them realize the full value of their security investments and improve their overall security posture.
Author of the Manning book on Azure Security, a practical guide to the native security services of Microsoft Azure that teaches how to use native security services of Azure to effectively improve system security and secure the various resources in the environment against threats.
I have a strong passion for cybersecurity, advancing women in tech and professional development. I'm very interested in building partnerships with other companies and cyber professionals to learn how they support, advance, and retain their cyber talent.
In addition to various technical certifications (21+ and counting), I've also received certifications from INSEAD and Kellogg School of Management.

Brian Honan
CEO
at BH Consulting
May You Live in Interesting Times.
This saying is supposedly from an old Chinese proverb. While the message may sound like a blessing, it is also deemed to be a curse. With the current rapidly changing threat landscape, new technologies such as AI, geopolitical challenges, and new regulations, Brian's talk will discuss how cybersecurity in now "Living in Interesting Times" and what we need to do to ensure the proverb turns out to be a blessing and not a curse.
Brian Honan is a recognised internationally expert on cybersecurity. He is CEO of BH Consulting an independent advisory firm on cybersecurity and privacy based in Dublin, Ireland. He formerly was a special advisor to Europol’s Cybercrime Centre (EC3), founder of Ireland’s first CERT, and sits on the advisory board of several innovative security companies. Brian has advised various government departments, companies of varying sizes, the European Commission, and the European Union Agency for Cybersecurity (ENISA) on matters relating to information security.

Christian Zäske
IT security consultant
at SySS GmbH
MeshHacks: Exploiting Linksys Intelligent Mesh from the internet | .tech
The days of hacking home routers are not over! Because every household, that wants internet access at their house, needs some kind of router, these could be a very interesting target, as there are millions of devices in use with a direct connection to the internet. One might think, that manufacturer should take extra care to make them as secure as possible, but apparently there is still room for improvement. A lot of room.
This presentation will show the accidental discovery of the most dangerous vulnerability type a device, especially a home router, can have: the unauthenticated remote code execution over the internet. It will not only focus on the technical part but also a practical example of how manufacturers should not respond to responsible disclosure.
Be curious about non existing input validation resulting in various outcomes, a lot of "Wait... what?" moments and the difficulties of responsible disclosure.
Christian Zäske is an IT security consultant for the pentest company SySS GmbH located in Germany. By starting his Bachelor's degree in computer science in cooperation with SySS GmbH in 2020, he turned his hobby into his profession: Security research. Being passionate about embedded security, he specialized in analyzing hardware of various types. From tiny hearing aids to full size EV charging stations.
Cristian Cornea
| .tech

Cristian Cornea
Founder
at Zerotak Security
Bypassing Anti-Virus and EDR using BadUSB | .tech
Agenda for the Cristian’s presentation: - AMSI Bypass Development - Execution Policy Bypass - Payload Runner Development - Deploying Attack using BadUSB - Post-Exploitation Persistence - DEMO – Prevention. During this presentation, we will take a look over how we can bypass most Anti-Virus detection using a payload embedded on a BadUSB device, resulting in a silver bullet for gaining initial access inside a victim network. Demo will be also included during the presentation.
Cristian is founder @ Zerotak Security & President @ Romanian Cyber Security Training Centre of Excellence. Providing pentesting & security consultation for clients all over the world: Australia, U.S., U.K., Middle East, Singapore, India, Central Africa, Europe.

Dalibor Gernhardt & Goran Polonji
Certified Wargame Designer / cybersecurity auditor
at Croatian Military Academy / Utilis Ltd.
Wargaming in the Cyber Domain: Challenges, Limitations, and Hybrid Approaches | .lead
When technical defenses and SOC procedures fail, the hardest part begins: making the right decisions under pressure. Cyber wargames are structured crisis simulations that expose gaps in procedures and decision-making that technical drills alone cannot reveal. From whether to isolate entire systems, to how and when to communicate with regulators or the public, wargames prepare organizations for rare but foreseeable “Gray Swan” events – scenarios that may not happen often, but can have devastating impact. In this talk we will explore why classical wargames are difficult to adapt to the cyber domain – from the non-linearity of time to the heavy dependence on expert moderators – and present a hybrid approach. Using the Cyber Conflict Simulator, we demonstrate how technical emulation and automated adjudication can bridge cyber ranges and classical wargames, reducing cost and reliance on scarce expertise. The result: scalable and realistic exercises that combine technical depth with management-level decision-making.
Dalibor Gernhardt is a Certified Wargame Designer (Naval Postgraduate School, US Army War College, US Center for Army Analysis) and PhD candidate at FER Zagreb. Goran Polonji is a cybersecurity auditor and co-developer of the Cyber Conflict Simulator, with extensive experience in cyber conflict simulation and hybrid approaches to training in complex environments.
Davor Perat
Senior Technology Consultant
at MBCOM Technologies
Addressing Modern Cybersecurity Challenges with Consolidated Cloud Platform | .ops
Unified cybersecurity platform are here to help organizations address modern challenges such as cloud adoption, remote work, and advanced threats. It integrates Zero Trust principles, offering secure access to applications and data from anywhere while preventing insider and external attacks. By combining endpoint, network, email, and information protection with strong data loss prevention (DLP) and threat intelligence, the platform reduces complexity and provides consistent policy enforcement across hybrid environments. This allows enterprises to protect sensitive data, detect and respond to evolving threats, and stay compliant with regulatory requirements in a rapidly changing threat landscape.
Davor Perat is a Senior Technology Consultant at MBCOM Technologies, specializing in enterprise security and digital transformation. With extensive experience in cybersecurity, endpoint protection, and data governance, he helps organizations design and implement solutions that strengthen resilience against evolving threats. Davor is recognized for his deep technical expertise, strategic approach to IT challenges, and ability to bridge business needs with advanced technology solutions.

Dejan Grubić
Team Leader of T2 and T3 Analysts
at Marlink Cyber
Incident management - best practices from field | .ops
In an era of escalating cyber threats, effective Cyber Incident Management is critical to safeguarding organizational assets and maintaining operational continuity. With growth in complexity and frequency of cyber threats, technical teams play a vital role in ensuring swift and effective Incident Management. This presentation explores the structured approach to identifying, managing, and mitigating cybersecurity incidents. It outlines the key phases of the incident response lifecycle—preparation, detection and analysis, containment, eradication, recovery, and post-incident review. Attendees will gain insights into best practices, frameworks, the role of automated tools, and the importance of cross-functional coordination. Real-world case studies and emerging trends will be discussed to highlight how proactive incident management can reduce impact, enhance resilience, and ensure compliance in an increasingly complex digital landscape.
Dejan Grubić, IT expert with long experience in creating virtual and cloud IT environments. He gained experience and knowledge through work for large system integrators in the region and as a regional representative of global companies in the field of virtualization, security solutions and data protection. Currently, as the head of the Cybersecurity Incident Response Team within Marlink Cyber, he encounters various types of incidents that occur globally, not only within the Adriatic region. He will try to translate the experiences gained during these incidents into his presentation.

Dinko Korunić
Principal Cloud Architect
at HAProxy Technologies
eBPF: Features, capabilities and implementation | .tech
The talk explores the powerful extended Berkeley Packet Filter (eBPF) technology. eBPF allows developers to run sandboxed programs in the Linux kernel without changing kernel source code or loading kernel modules. The talk covers key features such as network traffic monitoring, performance profiling, and security auditing. It also discusses the capabilities of eBPF, including its flexibility, safety, and efficiency in optimizing system performance. Additionally, the implementation part explains how eBPF programs are written, verified, and executed, offering insight into its architecture and use cases in production systems.
Dinko Korunic is Principal Cloud Architect at HAProxy Technologies and an accomplished IT professional with over two decades of experience in systems engineering, networking, and IT management. His expertise spans high-performance computing, Unix/Linux administration, and open-source technologies. Dinko has held roles in systems architecture, leading the design and implementation of complex infrastructure solutions for enterprises, particularly in network security, optimisation, and traffic management. He has contributed to projects across industries, including telecommunications and financial services. His educational background includes a degree in Computer Science, and he is highly skilled in system and application programming in C, C++, Perl, Python, Java, Rust and Golang. He is also actively maintaining a number of smaller open source projects.

Dirk Schrader
Field CISO EMEA / VP Security Research
at Netwrix Co.
A blueprint to protect your AD using NIST CSF 2.0 | .lead
The lecture will talk about the lifecycle of the AD, the lifecycle of identities, and how attacks are crossing these cycles. The main message conveyed is about how to embed preparation and prevention into those lifecycles, what role governance is going to play and how to identify areas where one can improve the cyber resilience of the AD environment.
Being a native of Germany, Dirk brings more than 25 years of delivering IT security expertise at a global scale. His work focuses on advancing cyber resilience as a sophisticated, new approach to tackle cyber-attacks faced by governments and organizations of all sizes for the handling of change and vulnerability as the two main issues to address in information security. He has published numerous articles in German and English about the need to address change and vulnerability to achieve cyber resilience, drawing on his experience and certifications as CISSP (ISC²) and CISM (ISACA).

Dmitri Belotchkine
Technical Director
at TXOne Networks
Deep Dive into securing critical OT infrastructure | .ops
Operational environments and critical infrastructure are being hit by cybersecurity incidents on a regular basis. More and more of them cause damage far outside of one company, reaching out to the national levels and impacting the people and environment. We have also seen “friendly fire” incidents caused by traditional IT security tools implemented in OT. In this session we will quickly look at the attack vectors and techniques observed in the cybersecurity incidents on OT and discuss why we fail to address them properly on the shop floor, and why using conventional IT security strategy and tools is not enough.
How to extend cyber physical security strategy in OT beyond the air-gap concept and deeper into the process and process control networks. We will also discuss the ways to do it without adding additional operational risks that can cause downtime and productivity loss.
Dmitri Belotchkine is a seasoned cybersecurity professional with a more than 25 years experience in IT and OT cybersecurity industries with a focus on High Tech and Manufacturing. Dmitri worked for large international system integrators and service providers such as Atos and Wipro as well as security products vendors. Before joining TXOne Networks last 7 years Dmitri spent at Trend Micro working with solutions and products for security of OT, Industrial IoT and 5G networks.

Domagoj Ćosić
Cyber Security Consultant
at A1 Hrvatska
Cybersecurity Challenges: Why Testing and Validation Matter | .ops
In this presentation, we will explore the fast-changing world of cybersecurity, examining why traditional security approaches are no longer sufficient. We will address the challenges organizations face in managing security tools and share insights on how to enhance resilience through automated security validation. Additionally, we will provide real-world examples that demonstrate why regular testing and validation of security measures are essential for staying ahead of evolving threats.
Bio:
My journey in the world of technology and information security started with a passion for computer engineering, which led me to pursue both a Bachelor's and Master's degree at the Faculty of Electrical Engineering in Osijek.
After completing my education, I began my professional career, gaining valuable experience across multiple organizations. I worked as a Systems Engineer for companies like Hrvatska Pošta and Infodom, where I managed VMware and Hyper-V environments, as well as Microsoft 365 administration, among other tasks. My role at Hrvatski Telekom allowed me to dive deeper into corporate services, where I provided technical support, participated in gap analysis, and contributed to the implementation of GDPR compliance measures, ensuring that data protection standards were met across the organization. Additionally, I oversaw various system integration tasks, enhancing the efficiency and security of corporate IT environments.
Currently, I am a Cyber Security Consultant at A1 Hrvatska, where I’m responsible for advising clients on the best cybersecurity solutions to meet their needs. I guide them through selecting appropriate technologies and strategies, such as NDR, EDR, and XDR, ensuring they have the most effective defenses in place. In addition to recommending solutions, I offer clients the best practices from the industry, helping them implement proven strategies that enhance their overall security posture and align with their business goals. This way, I ensure that each solution is not only technically sound but also tailored to their specific requirements.
My journey continues as I seek out new challenges and opportunities in the rapidly evolving world of cyber security, always striving to stay ahead of the curve and contribute to the success of the organizations I work with.

Dr. Marko Horvat
Assistant Professor at the Department of Applied Computing
at FER
When Cybersecurity Enters the Quantum Triangle: Quantum Computers, Quantum and Post-Quantum Cryptography | .ops
Quantum cryptography utilizes the fundamental laws of quantum mechanics to establish secure communication channels between different entities. One such use is Quantum Key Distribution (QKD), which facilitates the creation of a confidential shared key for the purpose of encrypting and decrypting messages. The presence of quantum features such as superposition and entanglement makes eavesdropping detectable and prohibits replication of quantum states. In theory, if the physical execution is excellent, this technology offers security that cannot be compromised. Nevertheless, the widespread use of quantum technologies is currently hampered by practical obstacles, including the attenuation of signals in optical fibers and the preservation of quantum states across extended distances.
Numerous cryptographic techniques in contemporary times rely on the challenge of factoring large numbers and calculating discrete logarithms. However, Shor's algorithm can swiftly factor numbers on a quantum computer, undermining conventional encryption methods like RSA and ECC. The QKD technique has been proposed as a solution to this issue. The first such protocol, known as BB84, was introduced in 1984 by Charles H. Bennett and Gilles Brassard. The BB84 protocol utilizes two distinct communication channels: a public channel and a quantum one, specifically an optical cable. It also employs various photon polarizations to facilitate the transmission of information. These initial solutions have been improved over time with BB91 protocol and other approaches.
More recently, another promising approach has been proposed, post-quantum cryptography which to cryptographic algorithms designed to be secure against the potential capabilities of quantum computers. The goal of post-quantum cryptography is to develop new methods of encryption and key exchange that would remain secure even in the age of quantum computing.
In the field of post-quantum cryptography, numerous potential algorithms have emerged as candidates that have the ability to withstand attacks from quantum computers. Several algorithms, such as BIG QUAKE, BIKE, Ding Key Exchange, GeMSS, HQC, LIMA, NewHope, NTRUEncrypt, Picnic, RSA-Encryption, and SPHINCS+, among others, already exist or are under development.
The emergence of quantum computing poses a significant challenge to existing encryption techniques, necessitating the adoption of post-quantum cryptography across multiple industries. In the context of secure communications and financial transactions, it functions as a protective measure against potential quantum-based security risks in the future. Cloud storage and Internet of Things (IoT) devices provide an increasingly robust security framework to mitigate the risks of unwanted access and cyberattacks. The utilization of this technology enhances the process of verifying digital identities, reinforces the tracking of supply chains, and guarantees the preservation of patient confidentiality within the healthcare sector. Furthermore, it serves to safeguard the integrity of electronic voting systems and decentralized networks such as blockchain. Post-quantum cryptography plays a crucial role in upholding digital security in a future characterized by the widespread adoption of quantum computers.
The talk will focus on the difficulties and solutions that quantum computing brings to the world of cryptography.
Dr. Marko Horvat is currently an Assistant Professor at the Department of Applied Computing at the University of Zagreb's Faculty of Electrical Engineering and Computing (FER). He graduated in 1999, with a MSc degree in 2007 and a PhD in 2013 from FER, specializing in artificial intelligence and mobile computing. After graduation, he gained 10-year professional experience in the ICT sector, as a software development engineer, software architect, project manager and IT department manager. He serves as a project manager, researcher and expert in a number of national and EU scientific projects. Previously, he worked as a lecturer, senior lecturer, study program supervisor, and vice-dean for science, international cooperation, and new study programs at the Technical University of Zagreb (TVZ), where he also founded the AI Lab.
Dr. Horvat has authored or co-authored more than 90 scientific papers during his academic career and has developed a number of university and professional instructional manuals and educational materials. In addition, he supervised over 80 BSc and MSc dissertations in informatics and computer science. He is engaged in editorial and review activities, serving on many editorial boards of international journals and conference program committees. His primary research interests are in artificial intelligence and machine learning, particularly in the areas of automated reasoning, knowledge representation, information retrieval, affective computing, and semantic web.
Marko Horvat is an active promoter of science and STEM education, regularly participating in educational activities and making media appearances speaking about a wide range of topics covering computer science, artificial intelligence, and the impact of disruptive technologies.
He is a Senior Member of the IEEE professional association and vice-chairman of the Croatian section of the IEEE Department of Management in Technology and Engineering. He is currently the Chairman of the Scientific Advisory Board of the Croatian Mine Action Center - Center for Testing, Development, and Training (HCR-CTRO) LLC.

Dubravko Hlede
Senior Technology Consultant, Adriatic
at MBCOM Technologies
XDR: Reduce Risk and Protect from Modern Threats | .ops
Explore how advanced security solutions are pushing the boundaries of traditional threat detection by delivering broad, deep, and context-rich data. This presentation will showcase how high-fidelity telemetry uncovers sophisticated adversarial tactics, tracking threats as they target endpoints, networks, identities, and more. Learn how these next-generation tools empower security teams to detect and respond to attacks in real-time, providing the visibility and insight needed to outmaneuver even the most advanced cyber threats.
Dubravko Hlede is a seasoned professional with extensive experience across industries such as finance, automotive, and research and development. He is now focused on applying his expertise on the vendor side, specializing in security and management solutions. With a proven track record of driving results and enhancing operational efficiency, Dubravko is dedicated to helping organizations safeguard their assets and streamline operations

Filip Barišić
Works
at National Cybersecurity Centre (NCSC-HR)
Legal framework for cybersecurity in the Republic of Croatia | .lead
On 15 February 2024 the Cybersecurity Act entered into force (Official Gazette No 14/24.) transposing into national law the EU NIS2 Directive (Directive (EU) 2022/2555 on measures for a high common level of cybersecurity across the Union). The Cybersecurity Act introduced a new, more comprehensive framework for the management of cybersecurity in the Republic of Croatia. The Act stipulates the procedures for categorisation of essential and important entities, regulates the obligations of essential and important entities in the implementation of cybersecurity requirements, defines the framework for carrying out cybersecurity audits and self-assessments, regulates all issues relevant for carrying out expert supervision of the implementation of cybersecurity requirements, and ultimately prescribes sanctions for non-compliance with prescribed obligations. Also, this lecture will provide information about the SK@UT community. SK@UT is the national system for detecting cyber threats and protecting cyberspace through a distributed network of sensors and cybersecurity tools. It helps protect the most critical organizations in the Republic of Croatia, including state authorities, critical infrastructure operators, and private sector entities of special interest to the Republic of Croatia.
Filip Barišić, M.Sc. in Electrical Engineering and Information Technology, graduated in 2018 from the Faculty of Electrical Engineering and Computing (FER), University of Zagreb. Also, in 2022 he completed postgraduate specialist study in Foreign Policy and Diplomacy at the Faculty of Political Science with a focus on cybersecurity policies. Since 2018, he has worked at several institutions, private and public ones. Right now, he works at the National Cybersecurity Centre (NCSC-HR).

Fyodor Yarochkin
Senior Researcher, Forward-Looking Threat Research Senior
at Trend Micro
Attacks on Cyber-Physical Devices: from cybercrime to espionage
With the widening segmentation and geo-fencing of the Internet and the explosive growth in number of cyber-physical devices, these devices become a lucrative target for criminal groups and state-sponsored threat actors alike. Often placed at the edge of organizations, devices such as digital cameras, smart building monitoring equipment, and even the city surveillance infrastructure are often targeted as attractive pivoting points and sources of on the ground information of the physical surroundings. In this presentation we discuss the risks of exposure of cyber-physical monitoring infrastructure, and attack patterns that we have identified in the wild. Further, we disclose several unconventional ways that attackers have used in order to identify and exploit such infrastructure and even build malicious overlay networks on the top of them. The presentation discloses some of previously unknown security issues with camera deployments and illustrates it with real-life war stories from different parts of the world
Fyodor Yarochkin is a Senior Researcher, Forward-Looking Threat Research Senior at Trend Micro with a Ph.D. from EE, National Taiwan University. An early Snort Developer and Open Source Evangelist as well as a Programmer, his professional experience includes several years as a threat investigator and over eight years as an Information Security Analyst.

Gábor Hirsch
Regional Sales Manager
at Thales
What else can a data security platform be used for? | .tech
Thales, one of the world's leading data security vendors, offers its customers several encryption and other data security solutions, but what happens when engineering invention overrides product development and the hidden functions of the solutions are revealed? The presentation is about such a story.
Gábor Hirsch graduated at Bánki Donát Technical Collage as information technology engineer and teacher. In the last 20 years I held on a lot of manager positions in information security and network security companies.
Among others he established and lead the Check Point distribution and IT security business unit in DNS Hungary (today is Arrow ECS) and as business development manager of Cisco Hungary he responsible on the success of the Cisco security products. He was the first employee of Fortinet in Hungary and I built the channel, brand and the team. Parallel his business carrier he took part in professional activities: he was member of Check Point Advisory Council, from 2008 till 2018 he was the leader of the information and IT security workgroup at IT Association of Hungary, and he was associate lecturer of King Sigismund University (today Milton Friedman University) and University of Public Service.
Before he joined to Thales as Regional Sales Manager he managed several data security and information security projects as independent advisor, worked as DPO and collaborated GDPR related projects in other advisories like PriceWaterhousCoopers.

Goran Polonji and Dalibor Gernhardt
Security specialists
at Utilis Ltd. / Croatian Military Academy
NIS2 – Tackling Incident Response Challenges with Cyber Conflict Simulator
The NIS2 Directive, the latest iteration of the Network and Information Systems Directive, aims to strengthen cyber resilience across the European Union (EU), particularly for operators of essential and critical infrastructure. The new version of the directive applies to a broader spectrum of essential service providers and digital service operators, establishing two key categories of entities: "essential entities" and "important entities," both of which must comply with NIS2's rigorous requirements.
However, what challenges do organizations face when it comes to effective Incident Response Team (IRT) training, and how can simulations elevate the learning experience and drive improvements in response tactics? These critical questions will be the focus of our workshop.
NIS2-regulated organizations often manage complex, interdependent IT and OT infrastructures, with many having highly critical IT environments. Their biggest challenge? Ensuring digital resilience and incident-readiness. But what happens when an incident occurs? How do you handle it effectively while staying compliant with NIS2?
In this hands-on workshop, participants will be guided through an immersive incident response process within a fictional essential entity, Fictional Essential Service Organization (FESO). FESO’s complex IT and OT infrastructure serves as the backbone of its operations and services. During the workshop, FESO will face a cyber attack led by an unknown attacker. Using Cyber Conflict Simulator, we will collaboratively explore the most effective tactics, techniques, and procedures (TTPs) for managing the incident, all while ensuring compliance with NIS2.
This workshop is designed for cybersecurity specialists and managers from organizations expected to be categorized as "essential" or "important" entities under NIS2. However, it is equally relevant to any company interested in enhancing its incident management processes. The workshop will provide real-world insights and strategies to help teams improve their response capabilities.
Workshop Highlights:
- Realistic Cyber Incident Simulation: Hands-on experience responding to a simulated cyber attack within FESO’s complex IT/OT environment.
- NIS2 Compliance Focus: Practical exploration of how regulatory requirements influence incident response strategies.
- Role-based Engagement: Participants will be assigned roles that mirror their real-world responsibilities, ensuring the workshop's relevance and applicability to their organizations.
- Collaborative Problem-Solving: Together, we will identify the best practices, challenges, and lessons learned from managing complex incidents.
The workshop will run for approximately two hours. We invite you to join us for this interactive session and take a step forward in strengthening your organization's cyber resilience and incident management.
Goran Polonji is an experienced Information Security Consultant and Cybersecurity Auditor at Utilis Ltd., with over 20 years of experience working with financial institutions and various industries to enhance information security and ensure regulatory compliance. As a domain expert, Goran is a key member of the Cyber Conflict Simulator development team. Throughout his career, he has focused on bridging the gap between business leaders and technology experts, promoting a deeper understanding of cybersecurity challenges. Goran is dedicated to aligning administrative and technical cybersecurity controls, helping organizations strengthen their defenses against evolving threats.
Dalibor Gernhardt is a lecturer in military defense and security intelligence at the Croatian Military Academy "Dr. Franjo Tuđman“, with over 12 years of experience in defense and security operations. In addition to his military role, Dalibor is a PhD candidate at the Faculty of Electrical Engineering and Computing in Zagreb. His doctoral dissertation focuses on the organization and implementation of simulation exercises in the field of cybersecurity, with an emphasis on practical applications and improving cyber resilience. Dalibor’s expertise in defense and cybersecurity gives him a unique perspective on bridging theoretical knowledge with real-world scenarios.
Cyber Conflict Simulator support team: Zdenko Ćorić (Utilis Ltd.), Vito Žuvanić (Utilis Ltd.), Dražen Barić (Utilis Ltd.), and Stjepan Groš (Faculty of Electrical Engineering and Computing, FER).

Goran Polonji and Dalibor Gernhardt
Security specialists
at Utilis Ltd. and Croatian Military Academy
DORA - Testing ICT response and recovery plans with the Cyber Conflict Simulator
It is common knowledge that in the year 2023, cyberattacks have claimed the top spot as the most significant business risk, and this trend is likely to persist in the years ahead.
The newly introduced EU regulation, known as the Digital Operational Resilience Act (DORA), specifically addresses this issue within its Regulatory Technical Standards (RTS) outlines the requirement for financial entities to incorporate provisions in their ICT business continuity policies pertaining to the development, testing, and review of ICT response and recovery plans. Notably, the first scenario detailed in RTS revolves around the subject of "cyber-attacks."
We invite you to join our workshop, where you will gain insights into how to enhance and test your cyber incident response and recovery plans using the Cyber Conflict Simulator.
During this workshop, participants will assume various roles, such as incident handlers, business service owners, and members of the management board, all representing a fictional entity called Generic Financial Institution (GFI). GFI will face a sophisticated attack orchestrated by an Advanced Persistent Threat Group (APT). Your collective mission, along with fellow participants, will be to ensure the continuous operation of the business, simultaneously detecting the attacker within the network, responding effectively, and facilitating the recovery of the ICT infrastructure, enabling GFI to resume normal operations. Participants will have the opportunity to apply their existing knowledge of ICT response and recovery plans and, hopefully, acquire new insights from the trainer and the CCS support team.
This workshop extends its relevance beyond financial institutions. Cyber specialists and managers in various industries and government institutions are well aware that NIS/NIS2 Directive incorporates identical requirements for their ICT infrastructure. Therefore, participation will be equally engaging for them.
The duration of the workshop will extend up to two hours, contingent on participant engagement and the pace at which the incident is addressed. To maximize the workshop's effectiveness, registered participants will be assigned roles tailored to their real-world responsibilities within their respective organizations.
If you are a registered DEEP attendee, please be free to reserve your workshop seat at https://forms.gle/LZwk6FA4KCjLv7kC8.
Trainers professional bio: Goran Polonji is an information security consultant and cybersecurity auditor in Utilis Ltd. Last twenty years he is working with financial institutions and industry in improving information security posture and fulfilling regulatory compliance. Goran is a member of Cyber Conflict Simulator development team as a domain expert. He is continuously trying to build understanding between business and technology experts about cybersecurity and to fill the gap between administrative and technical cybersecurity controls.
Dalibor Gernhardt is a lecturer in military-defense and security intelligence science and art and teaching at the Croatian Military Academy. For the last 12 years, he has been doing various jobs in the defense and security domain. In addition, he is PhD student at the Faculty of Electrical Engineering and Computing in Zagreb on the subject of computer security. He is preparing a doctoral dissertation on the topic of organization and implementation of simulation exercises in the field of cyber security.
Along with two main trainers, there will be the CCS support team: Zdenko Ćorić (Utilis Ltd.), Vito Žuvanić (Utilis Ltd.), Stjepan Groš (FER).

Igor Brumen
Information Security Specialist
at Avola Solutions
GenAI as a new data leakage channel: what can DLP really protect? | .ops
Generative AI tools have quickly become part of everyday work. Users rely on them to summarize documents, generate reports, write emails, analyze code, and speed up tasks that used to take hours. But the same workflows that improve productivity can also become new paths for sensitive data to leave the organization.
What happens when sensitive information is shared with an AI tool? How can organizations maintain visibility and control without blocking productivity? And where do technical controls provide real protection — and where do their limitations begin?
The session will focus on practical GenAI usage scenarios and the challenges they create for data protection programs. Igor will discuss how organizations can improve visibility, apply meaningful controls, and reduce the risk of sensitive data exposure across the different ways employees use AI tools — while also addressing the practical limitations security teams need to understand before relying on any single layer of protection.
The goal is not to claim that any single control can solve the GenAI data leakage problem. Instead, the session will provide a practical technical view of what can be protected, what cannot be fully controlled, and how organizations can reduce risk while still enabling the productivity benefits of AI.
Igor Brumen is a cybersecurity engineer with 18 years of experience in IT and cybersecurity, focusing on IT infrastructure, endpoint security, identity management, MFA, data protection, encryption, and enterprise security architectures. He has more than 8 years of experience in digital forensics and hands-on experience with DLP implementations, detection scenarios, policy design, incident investigation, and securing hybrid enterprise environments.

Igor Tomičić
Lead Auditor 27001&22301, Security consultant and Associate Professor
at Faculty of Organization and Informatics
Sociotechnical Auditing: What Your Checklist Isn’t Telling You | .lead
Audits often promise assurance - but in practice, checklists can conceal more than they reveal. This session challenges traditional views of information security audits by exploring them as sociotechnical systems: dynamic interactions between people, processes, and technology. While ISO 27001 and similar frameworks provide structure, real assurance requires more than verifying documentation or tool outputs.
We’ll examine how human behavior, organizational culture, and technical blind spots shape audit outcomes, and why surface compliance often masks deeper risks. You'll hear about practical techniques to detect performative compliance, break through siloed defensiveness, and uncover systemic non-conformities that traditional audits miss.
Whether you're an auditor, compliance lead, or engineer facing an audit, this talk should boost your audit instincts - and help you see what your checklist isn’t showing you.
Igor is an information security professional whose career bridges academia and practice. He is an Associate Professor at the University of Zagreb, where he works as Head of the Department of Computing and Technology, develops and teaches security courses, and has published over 70 scientific papers with 600+ citations. In parallel, he runs a security consulting and auditing firm, applying his expertise to real-world challenges. His interests are broad but center on the fun stuff: offensive security, applied cryptography, data security, social engineering, and GRC, with a healthy dose of IoT and AI research mixed in.
He also holds ISO 27001 and ISO 22301 Lead Auditor certifications, which he applies by digging into organizations, systems, processes, assets, and people - balancing professionalism and approachability while still delivering the tough truths that audits often uncover.

Igor Tomičić
Associate Professor
at Faculty of Organization and Informatics
Raw and Uncensored: How (InfoSec) Science Works - and How to Exploit It | .lead
A raw, practical walkthrough of how InfoSec science actually works: what research can support, what remains uncertain, and why security evidence is often more fragile than vendor claims suggest. We start with the basics of scientific reasoning, hypothesis testing, uncertainty, and peer review, then move into the ugly parts of cybersecurity research: adversarial environments, weak or outdated datasets, unrealistic benchmarks, misleading metrics, poor reproducibility, and the gap between lab results and operational reality. From there, we look at how cautious, conditional research findings get compressed into confident (vendor) claims about accuracy, AI, detection, automation, and risk reduction. Attendees might leave with a more practical way to read security papers, challenge product claims, interpret metrics, and separate meaningful evidence from scientific-looking noise.
Igor is an information security professional whose career bridges academia and practice. He is an Associate Professor at the University of Zagreb, where he works at the Department of Computing and Technology, develops and teaches security courses, and has published over 70 scientific papers with 600+ citations. In parallel, he runs a security consulting and auditing firm, applying his expertise to real-world challenges. His interests are broad but center on the fun stuff: offensive security, applied cryptography, data security, social engineering, and GRC, with a healthy dose of IoT and AI research mixed in.
He also holds ISO 27001 and ISO 22301 Lead Auditor certifications, which he applies by digging into organizations, systems, processes, assets, and people - balancing professionalism and approachability while still delivering the tough truths that audits often uncover.

Ilija Jozinović
IT Infrastructure Manager
at Orbico Group
How to achieve "real-time" system visibility and security in a large company? | .ops
This session focuses on the successful implementation of the XDR solution, which enabled us to achieve real-time system visibility across 20 countries and over 100 locations within the Orbico Group and more than 8,000 employees. Without the right XDR solution, IT hygiene practices and other security measures there is no reduction in Cybersecurity risk for organization.
Ilija Jozinović currently performs the role of an IT Infrastructure Manager in Orbico Group where he is responsible for managing the proper IT infrastructure of the organization and he’s responsible for Support, Systems, Networking and CyberSecurity teams. He has more than 15 years of experience in IT.
Ivan Ivković
Presales engineer
at Group-IB
Advance Your SOC Maturity Through Intelligence-Led Security Operations | .ops
This session examines key threat intelligence use cases that support the transition from reactive to proactive cybersecurity operations. It demonstrates methods for continuous mapping and assessment of external digital assets to uncover vulnerabilities, shadow IT, and misconfigurations from an adversarial perspective, enabling high-impact remediation. The session also highlights the application of threat intelligence to derive actionable insights into tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs), enhancing threat detection, investigation, and response capabilities. Additionally, it showcases the critical role of dark web investigations in exposing hidden adversaries.
The presentation is delivered in a live demonstration format.
Ivan Ivković is an experienced cybersecurity leader and engineer with over 15 years of experience in engineering, architecture design, consulting, and presales. He began his career as a systems engineer and quickly developed a strong interest in cybersecurity. His expertise includes working with various modern technological security solutions such as NGFW, ATP, EDR, SIEM, DLP, ASM, CTI etc. He is experienced in building and growing SOC (Security Operations Center) services and teams in the role of SOC Manager. Currently, his primary focus is enabling partners and clients in the field of Threat Intelligence working as a Presales Engineer at Group-IB.
Ivan holds numerous certifications and titles, including SANS Operational Cybersecurity Executive, GIAC Security Operations Manager (GSOM), SOC-CMM Certified Assessor etc.

Ivan Pepelnjak
Independent network architect
at ipSpace.net AG
Use Digital Twins to Test Disaster Recovery Designs | .tech
Numerous disaster recovery designs promoted by infrastructure vendors and Thought Leaders ignore the laws of physics (non-zero latency and limited bandwidth) and thus work best in PowerPoint. Even worse, many disaster recovery designs are never tested because we’re too afraid to pull the plug and wait to see what happens.
However, with the ubiquitous virtualization, it’s possible to build a pretty realistic, scaled-down replica of your environment (containerizing your applications makes it even easier) that allows you to test application behavior and performance under various failure scenarios.
This presentation will focus on the networking aspects of that idea, explain how we can emulate the laws of physics (adding artificial latency or bandwidth constraints), and how we could test the impacts of infrastructure failures on end-to-end connectivity.
Ivan Pepelnjak, CCIE#1354 Emeritus, is a 30-year veteran of the networking industry, with 25+ years of experience in designing, installing, troubleshooting, and operating large service provider and enterprise WAN and LAN networks. He is currently an independent network architect at ipSpace.net AG, focusing on network automation, software-defined networking, large-scale data center and network virtualization technologies, and advanced IP-based networks.
Ivan is the author of a series of highly successful webinars and online courses. His books published by Cisco Press include MPLS and VPN Architectures and EIGRP Network Design.

Ivan Pepelnjak
Independent network architect
at ipSpace.net AG
Disaster Recovery Myths and Reality | .tech
Infrastructure (virtualization, storage, and networking) vendors love to tell you how to use their products to implement disaster recovery or high-availability architectures without touching the applications. Most of those solutions work best in PowerPoint and vendor whitepapers; they could cause a disaster in production deployments.
In this presentation, we’ll explore several (somewhat disguised) real-life disasters caused by that mentality and end with a few recommendations that have been proven to work in mission-critical deployments.
Ivan Pepelnjak, CCIE#1354 Emeritus, is a 30-year veteran of the networking industry, with 25+ years of experience in designing, installing, troubleshooting, and operating large service provider and enterprise WAN and LAN networks. He is currently an independent network architect at ipSpace.net AG, focusing on network automation, software-defined networking, large-scale data center and network virtualization technologies, and advanced IP-based networks.
Ivan is the author of a series of highly successful webinars and online courses. His books published by Cisco Press include MPLS and VPN Architectures and EIGRP Network Design.

Ivan Pepelnjak
Independent network architect, webinar author and prolific blogger
at ipSpace.net AG
Internet Routing Security | .tech
While we had the necessary means and technologies to significantly enhance the routing and packet forwarding security in the Internet for years if not decades, we’re still facing BGP hijacks and amplification DDoS attacks on daily basis.
This talk will describe some of the reasons for this dismal state of affairs, the steps one can take to increase the Internet routing security, and the MANRS framework that can guide you on that journey.
Ivan Pepelnjak, CCIE#1354 Emeritus, is a 30-year veteran of the networking industry, with 25+ years of experience in designing, installing, troubleshooting, and operating large service provider and enterprise WAN and LAN networks. He is currently an independent network architect at ipSpace.net AG, focusing on network automation, software-defined networking, large-scale data center and network virtualization technologies, and advanced IP-based networks.
Ivan is the author of a series of highly successful webinars and online courses. His books published by Cisco Press include MPLS and VPN Architectures and EIGRP Network Design.

Ivan Zelić
Information Security Specialist
at Marlink Cyber
Practical challenges in NIS2 implementations | .lead
NIS2 Directive transpositions impose regulatory obligations on a large number of entities to implement security controls that they have not previously encountered. In this presentation, attendees will gain insight into the key challenges companies face in efforts to achieve compliance, but also the ways in which these challenges can be overcome.
Ivan Zelić is an information security consultant with significant experience in IT auditing and IT GRC consulting. He is employed at Marlink, working on projects that help organizations achieve compliance with regulations and standards through the design and documentation of security controls and processes.

Ivona Loparić
Information Security Consultant
at Diverto
NIS2 – Europe's roadmap to Cyber resilience | .lead
Summary:
Is it just another regulation or will it have more profound impact? The Network and Information Systems Directive 2 (NIS2) represents a pivotal moment in the EU's approach to cybersecurity. While on the surface, it may seem like another set of rules, NIS2 is poised to reshape the digital landscape of Europe. With its expanded scope, stringent incident reporting requirements, and a renewed emphasis on cross-border cooperation, NIS2 isn't just about compliance – it's about forging a united front against cyber threats. NIS2 isn't just another regulation, it's the blueprint for safeguarding Europe's digital future. Join us in exploring the layers of this directive, from its regulatory core to its potential to fortify the resilience of our digital infrastructure.
Short professional bio:
Ivona Loparić is Information Security Consultant with 10 years of experience working as IT auditor and consultant. In her career, Ivona worked on various engagements related to compliance with regulatory requirements and standards related to information security, including NIS Directive, EBA / CNB guidelines and ISO/IEC 27001. Even though most of her engagements were related to financial sector, Ivona has experience with working for production, trade, utility and public sector. Some specific areas of Ivona’s interest are IAM (Identity and Access Management) and Social Engineering.

Jakov Vlašić
ICT Support Specialist
at A1 Hrvatska
Unlock Me If You Can: Exploring The Security Of Digital Systems | .tech
In this session, Jakov Vlašić, ICT Support Specialist from A1 Hrvatska will introduce a versatile tool for pentesting and hardware hacking. He’ll explain its key features, including RFID/NFC, infrared communication, sub-GHz, and GPIO interfaces. The talk will cover both legitimate applications of the tool as well as potential security risks in cases of misuse. Through recorded demonstrations, Jakov will showcase real-life scenarios of interacting with technologies we encounter every day. The goal of this lecture is to demystify how such tools work, highlight their role in the field of cybersecurity, and emphasize the need for effective protective measures. By combining expert commentary with practical examples, we aim to deliver both a technical deep dive and an engaging look at security in action.

Jasmin Azemović
Head of SecOps
at HTEC Group
Security challenges in the software development industry...what can go wrong? | .tech
Cyber-security as a broader form of protection of all IT resources has long ceased to be a luxury. On the contrary, it has become an imperative. Pandemic and geopolitical challenges contribute to this. The challenges we are facing are escalating on a daily basis. The result can be catastrophic consequences for your business: data breaches and leaks, ransomware, insider threats and the list goes on. The software industry is most important part of digital transformation of society and secure enough solutions are set as an obligatory requirement.
This session is intended for all those involved in software development process and decision makers (the private sector, government, and public institutions). Also, for everyone else who wants to hear about the experience from first line of defense.
Jasmin Azemović is a CISO, University Professor and ex. Dean. Professionally engaged in the areas of information security, privacy, forensic analysis and database systems for the last 20+ years. Currently leading the defensive security department within the HTEC Group. Author of the books: Writing T-SQL Queries for Beginners Using Microsoft SQL Server 2012, Securing SQL Server 2012 and SQL Server on Linux. Microsoft Security MVP and speaker on many IT conferences, events, and panels with more then 150 speaking engagements in the last 15 years.

Josip Franjković
Freelance security researcher
Maximising rewards and impact in bug bounties | .tech
Thirteen years since my first paid report to a bug bounty program, I have seen it all. This presentation will focus on evening the odds in the bug bounty field, maximizing rewards and avoiding the typical pitfalls when reporting security issues.
I will present a collection of real reports - low severity bugs turned critical, "N/A" reports that were in fact applicable and other interesting edge cases I've found myself in, along with general tips and tricks on increasing impact and getting your reports paid
Josip Franjković is a freelance security researcher and a "bug bounty hunter". Throughout his career he has reported over 200 verified vulnerabilities to companies like Facebook, Google, Microsoft, PayPal, Yahoo and others, with a main focus on authentication and authorization vulnerabilities.
Josip is a top hacker on PayPal's bug bounty program, and tops Facebook's whitehat list in the '17-'19 period. He has also participated in live hacking events around the world for PayPal, Yahoo and Facebook, where he was asked to find vulnerabilities in yet to be released software and hardware, winning two "Most Valuable Hacker" awards and placing among the top three participants multiple times.

Konstantin Shvetsov
Head of Information Security and compliance
at LOGEX
Exploring Serverless Threats | .tech
Understanding its unique security challenges is paramount as serverless computing revolutionizes application development. This presentation explores the evolving landscape of serverless threats, from data breaches to injection attacks. Delving into real-world cases, we dissect vulnerabilities arising from inadequate authentication, insecure deployment practices, and more. We will dive deeper into the real-world attack that occurred this summer and understand how we could prevent it or mitigate it. Attendees will gain insights into proactive measures such as strict access controls, continuous monitoring, and leveraging managed security services. By comprehending the intricate interplay of serverless architecture and security, this presentation equips professionals to build and maintain resilient, threat-resistant serverless applications in an increasingly interconnected digital ecosystem.
Konstantin is the Head of Information Security and compliance, a member of the Cloud Security Alliance, and has 18 years of experience in cybersecurity. The expertise includes serverless architectures, threat analysis, and implementing robust security frameworks for scalable cloud solutions.

Krešimir Pašiček
Senior Information Security Engineer
at Microblink
How to blend Automotive, Cloud and SaaS into a seamless security mix? | .tech
Modern vehicles, cloud applications, and SaaS platforms face many shared cybersecurity challenges. In this talk, Krešimir will guide the audience through securing CAN bus networks and over-the-air updates in electric cars, protecting SaaS platforms, and managing enterprise cybersecurity. Drawing from real-world experience across Rimac Technology, Sofascore, and Microblink, this presentation highlights common attack surfaces, effective prevention strategies, and practical lessons learned—providing valuable insights for technical professionals and decision-makers alike.
Krešimir Pašiček is a senior information security engineer passionate about building secure systems across industries. He’s worked on the cybersecurity of the Rimac Nevera hypercar, safeguarded SaaS applications at Sofascore, and now handles vulnerability management, device security, and infrastructure protection at Microblink. Whether it’s protecting vehicles, cloud environments, or digital services, Krešimir enjoys turning complex security challenges into practical solutions that work in the real world.

Kruno Jurlina
Process manager
at ATO Inženjering
Secure Programming and Integration of OT Systems - Good and Bad Practices | .tech
In industrial practice, mindsets such as “Don’t touch what works”, “Keep it simple”, or “It had to be finished yesterday” often prevail. While practical, this mindset significantly complicates - and in some cases completely prevents - the application of fundamental cybersecurity principles in control systems. An additional challenge lies in the lack of official guidelines and real-world examples for secure PLC programming, leaving engineers to rely on ad-hoc solutions and improvisation.
To help bridge this gap, the professional community has developed the “Top 20 Secure PLC Coding Practices” document, with related guidelines on secure system architecture currently in preparation. This presentation will provide a concise overview of the most relevant and impactful recommendations from these guidelines, illustrated with real-world examples of both good and bad practices. The aim is to raise awareness and encourage the adoption of more secure development practices within OT environments.
Kruno Jurlina holds a master's degree in electrical engineering and has more than 20 years of experience in developing, integrating and maintaining supervisory control systems in diverse industrial sectors. Since 2016, he has specialized in the field of operational technology (OT) cybersecurity and, since 2018, has held the ISA/IEC 62443 Cybersecurity Expert certification.
He has participated in numerous projects related to the cybersecurity of critical infrastructure, with a strong focus on the application of international standards and best practices. He was actively involved in the global initiative "Top 20 Secure PLC Coding Practices" and is the author of the Croatian translation of these guidelines. He currently leads the Cybersecurity and Digital Transformation program at ATO Inženjering d.o.o., one of the region’s foremost system integrators and the market leader in OT cybersecurity.
From the very beginning, he has been engaged with the Croatian Institute for Cybersecurity, where he currently serves as the Chair of the Committee for Industrial Control Systems Cybersecurity.

Leon Juranić
Security consultant
at Mend
Modern application security trends | .ops
Overview of an application security evolution from nineties till modern days from an expert with his hands deep in the application security dirt for the last 25 years, since his early teen years. Best approaches for your application security policy program from a person who single handedly developed state of the art SAST and DAST solutions used by Fortune 100 companies and discovered critical remote and local security vulnerabilities in the core of all members of the holy trinity, Windows, Linux and Mac, beside NASA and 150 other software vendors.
Leon Juranić is a security consultant at Mend where he works on improving application security products and an all-around hacker in his spare time. He has decades of experience in information security and application security. Among others, he founded Defensecode company, most famous for its DAST and SAST products. Defensecode was later acquired by WhiteSource/Mend. Leon has numerous 0-days in the high-profile software, vulnerability advisories and CVEs on his belt. He has been 3 times slashdotted.
Leon Schulze
| .ops

Leon Schulze
Associate Solution Engineer
at Carbon Black
Empower your SOC: An XDR story | .ops
VMware Carbon Black XDR shifts the balance of power away from adversaries and back to security teams. As the evolution of Carbon Black Enterprise EDR, our XDR delivers on modernizing the SOC by enabling rapid and accurate detection, visualization and analysis of endpoint, network, workload, and user data in context. Powered by VMware ContexaTM, Carbon Black XDR surfaces new results by preserving and extending the endpoint and network contexts during analysis and display.
Leon Schulze is a Security Solutions Engineer at Carbon Black, CEMEA. He is responsible for designing, implementing, and troubleshooting workload, endpoint, and cloud security solutions for various clients in central and eastern Europe. He has a natural flair for making complicated security topics accessible to everyone. Whether he's speaking to a room full of experts or educating novices, his unique storytelling approach turns complex topics into relatable narratives.

Luka Kladarić
Chaos Guru
Kill the Dev VPN | .ops
Developers constantly juggle VPN connections across multiple environments, creating headaches for security teams and compliance auditors. Traditional VPNs, once essential for remote access, now hinder productivity and security. Over-provisioned profiles, credential sprawl, and unclear access logs make it nearly impossible to track who accessed what. Real-world incidents—like lingering production access for ex-employees and audit failures due to missing logs—highlight the risks. Understanding how and why VPNs fail modern teams, let's explore emerging alternatives and show how organizations can turn developer access into a compliance advantage.
Luka Kladarić, aka the Chaos Guru, is a seasoned IT professional with over 20 years of experience in software development, cloud infrastructure, architecture, and security. He specializes in managing technological chaos by fixing and improving systems that others overlook. Luka has worked with notable global brands like DeviantArt, Noom, and Meetup. A remote work evangelist and tech leader, he is known for his ability to solve complex problems and optimize IT environments efficiently.

Luka Volarić
Information Security Specialist
at Avola Solutions
Zero-day headlines sell news, but IT hygiene saves the organization | .ops
Zero-day vulnerabilities cause panic and generate clicks, but the attacks that happen usually rely on much simpler weaknesses. No MFA? A server unpatched for two years? Half of your users with admin rights? In such an environment, an attacker doesn’t even need a zero-day exploit.
In this session, Luka will share real-world examples of where organizations truly lose the battle and how attackers take advantage of these ‘boring’ weaknesses. The focus is on IT hygiene, from patching and identity management to basic security measures, because these are the controls that stop most attacks.
Luka began career as IT helpdesk technician in a global corporation, later advancing to lead the helpdesk team before transitioning into system administration. From there, he worked as a sysadmin at a MSP, and today is focused on cybersecurity. Along the way, he has seen it all: lousy configurations, outdated systems with over 3 years of uptime, and users who click on suspicious links faster than a teenager can double-tap a TikTok video. Those experiences across different roles made it clear to him that the real battlefield lies in cybersecurity, where technology, people, and processes intersect.
Today, Luka works as an Information Security Specialist at Avola Solutions d.o.o., where his main responsibilities include endpoint protection, incident investigation, threat analysis, vulnerability management and developing proactive security services for our customers. What his career has taught him is simple: technology alone doesn’t guarantee security, it’s about discipline, awareness, and getting the basics right.

Lutz Wiechmann
International Senior Sales Engineer
at Enginsight
Scanning to Response: 100% EU made All-in-One Cybersecurity Platform in Action | .ops
Companies in Europe face growing cyber threats, tight budgets, and limited IT resources. Backdoors, supply chain vulnerabilities, and unaddressed weaknesses can quickly turn into serious risks.
This session will show how Enginsight helps companies manage cybersecurity from a single platform. It will feature a live demo, giving attendees a first-hand look at how continuous vulnerability scanning, automated penetration tests, IT monitoring, and compliance reporting work together to provide clear insights and practical workflows. Attendees will learn how to spot risks, prioritize actions, and maintain secure, compliant operations—without the need for large teams or expensive tools.
Lutz Wiechmann is a cybersecurity and IT expert with over five years at Enginsight, working with companies of all sizes, from small businesses to large enterprises. He has collaborated closely with IT teams, CEOs, and IT directors across healthcare, finance, manufacturing, and the public sector.
Through this experience, Lutz has developed a deep understanding of recurring IT and cybersecurity challenges that many companies and their MSSP partners face, giving him practical insight into real-world solutions and strategies.

Marin Jaram, Tihomir Maček and Marin Vidaković
Security engineer / Product Manager / Cloud solution architect
at Ingram Micro / Sedmi odjel
Good, Bad and Ugly Compliance in Public Cloud | .ops
From Orchestration and Automatization to safety of Vendor solution for Proactive reaction with real-time monitoring, fully audited controls for various aspects of security access to automated alerts and notifications of policy violations. Why using CloudBots for incident response empower and for automatic remediation.
Marin Jaram is a security engineer with 18+ years of experience in the field. From Developer cross System integration to Pre-Sales landed on cyber security in last 8 years and enjoy it from the bottom of his heart. Evaluate cyber security solution and in constant search for potential solutions for all business risks of our partners and clients.
Tihomir Maček is an experienced Product Manager with 7 years of expertise in the field of Cyber Security in the dynamic world of IT distribution, primarily at Ingram Micro, the world's largest player in this industry. His career is a testament to his commitment to excellence in the field of IT and Cyber Security product management. Beyond his professional life, Tihomir enjoys spearfishing, skiing, and playing football in his free time.
Marin Vidakovic is a cloud solution architect and security enthusiast with over 20 years of experience. He began his career as a developer, then moved into telecom and networking operations, and now leads a cloud consulting company that assists software developers on their journey to cloud-native applications.

Mario Blažević and Andrija Grgić
CISO / Information Security Consultant
at Diverto
Managed SOC in OT environments: no problem? | .tech
In the OT world, it's not about 'Ever tried? Ever failed? Try again, fail better!' It's more like 'Fail once, and you might not get another shot to innovate.' The adoption of an OT Security - Operations Center (OT SOC) has never been more crucial, especially with the NIS2 directive and its accompanying regulations knocking on our digital doors. But wait, integrating and managing OT SOC services within critical infrastructure? It's no walk in the park.
Join Diverto in this presentation as we unravel the challenges, share our experiences, and draw valuable conclusions. In the world of managed SOC in OT environments, we'll explore whether it's really a breeze or if there are hidden storm clouds on the horizon. Don't miss it!
Mario Blazevic is an experienced information security professional, with a strong emphasis on Industrial Control Systems (ICS) cybersecurity, particularly within the energy, traffic, and utility sectors. Specializing in NIS and ISA/IEC 62443 standards, Mario in Diverto manages complex cyber-security/information security projects and effectively communicates risks with stakeholders. In roles ranging from trusted advisor, auditor, to both externalized and internal Chief Information Security Officer (CISO), Mario has a proven track record of implementing diverse management systems in the fields of information and cybersecurity, as well as quality management. This ensures compliance with the NIS Directive, GDPR, and other regulatory requirements, alongside various standards and frameworks. With extensive auditing expertise and proficiency in information security frameworks like COBIT, NIST, and ITIL, Mario offers valuable insights, navigating the intricate landscape of information and cybersecurity challenges across diverse industries.
Andrija Grgić is a Senior Information Security Consultant at cybersecurity company Diverto ltd., where he focuses on challenges in OT/ICS landscape and critical infrastructure environments. Prior to Diverto, Andrija worked in IT Security and Systems Integration for 15 years. During that time, he has achieved top level certifications, including Cisco CCIE Security. Using this experience, Andrija is dedicated to pursue OT/ICS topics and bringing cybersecurity awareness to the next level. Highly skilled in designing and implementing IT/OT security architecture, Andrija is always ready to share his knowledge and experience. In his private time, he can be found usually jumping from one mountain peak to another.

Mario Blažević, moderator
Senior Information Security Consultant
at Diverto
Breaking the Chain - Navigating Cyber Incidents and Supply Chain Security
Note: this panel will be in Croatian, thus the following announcement is also in Croatian.
Panel će se održati 23.10, u vremenu od 11:30 do 13:00, na lokaciji Falkensteiner FORTIS CENTAR
Moderator panela je Mario Blažević, Diverto.
Gosti panela:
- Alen Delić, Spotme
- Aleksandar Klaić, Centar za kibernetičku sigurnost
- Milan Parat, HUB
- Saša Zdjelar, Reversing Labs
- Slaven Smojver, HNB

Mario Esposito
Director of Technical Sales
at Radiflow
Evolution of Threat Monitoring and Anomaly Detection in Critical Infrastructures | .ops
The digitalization of industrial environments demands advanced OT security solutions.
This session will examine how OT security has evolved from early signature-based detection to modern behavior-driven anomaly detection.
We will also cover practical strategies for building an effective OT SOC, including playbooks for risk-based alert prioritization.
Join us to learn how OT security evolved from signature-based detection to behavior-driven anomaly detection, and discover essential strategies for building an effective OT SOC.
Mario is Director of Technical Sales at Radiflow, a cybersecurity leader with over 10 years of experience in IT/OT security, risk management, presales leadership, and network engineering. Expert in end-to-end OT cybersecurity, from initial assessment to implementation and governance.

Mario Kozina
Chief adviser
at HNB
DORA Third-Party Risk: Regulatory Challenges for Financial Institutions and ICT Service Providers | .lead
The Digital Operational Resilience Act (DORA), effective from 17. January 2025, introduces stringent requirements for managing third-party ICT risks, creating significant challenges for both financial institutions and ICT service providers. This presentation will help financial institutions and ICT service providers to understand the key DORA requirements, navigate contractual provisions, cooperate effectively to mitigate ICT risks and improve resilience across the financial sector.
Mario Kozina is a Chief adviser at the Croatian National Bank (HNB) where he supervises how credit institutions manage IT risk. His professional interests lie in the areas of IT management, security, audit, outsourcing and provision of financial services. For the past few years, he has participated in the development of regulatory acts (at the HR and EU level) related to IT risk management and digital operational resilience of financial institutions. He graduated in computer science at FER and is CISSP and CISM in good standing.

Mario Kozina
Senior adviser
at HNB
DORA Regulation overview | .lead
Wide use of IT in financial institutions, increased complexity and occurrence of cyber incidents contributed to the growth of IT risk and the need for a stronger regulatory framework. Join this session to get an overview of the new EU Digital Operational Resilience Regulation – DORA that will apply from January 2025. Emphasis will be on DORA's requirements related to IT risk management and security testing.
Mario Kozina is a Senior adviser at the Croatian National Bank (HNB) where he supervises how credit institutions manage IT risk. His professional interests lie in the areas of IT management, security, audit, outsourcing and provision of financial services. For the past few years, he has participated in the development of regulatory acts (at the HR and EU level) related to IT risk management and digital operational resilience of financial institutions. He graduated in computer science at FER and is CISSP and CISM in good standing.

Marko Bobinac
Director of Strategic Alliances Payment and Trusted Services
at Thales Cyber Security Products
Next-Gen Crypto, Today | .ops
Join us as we unpack the current state of PQC, explore first implementation steps and real-world use cases, discover where Thales has already embedded PQC, and get to know the expanding ecosystem driving quantum-safe security.
Marko Bobinac is leading Thales’s Alliances in the area of Payment and Trusted Services. Through the 13+ years in Thales Marko was working with all Encryption, Key Management and Authentication solutions from Thales CPL is portfolio.
Marko has experience in Customer projects for securing Confidentiality, Integrity, Availability and Accountability with Network Encryption, Payment security solutions, modern PKI infrastructure, efficient Storage&File encryption, DB encryption, Data Anonymization and other encryption based solutions. He is also one of the pillars of Thales’s eIDAS strategy for both Authentication and Hardware Security Modules product lines.

Marko Bobinac and Daniel Danilovski
Director of Strategic Alliances Payment and Trusted Services / Manager of Professional Services
at Thales / Nextsense
The Future of Encryption: Uncovering Trends You Didn't Know You Needed to Ask About
Dive into the cutting-edge world of encryption with insights on quantum cryptography, confidential computing, Central Bank Digital Currencies (CBDC), and the innovative Signature Activation Module presented by Nextsense. Discover how these emerging technologies are shaping the future of digital security and privacy, and gain the knowledge you need to stay ahead in this rapidly evolving landscape.
Engage with interactive quizzes that will test and expand your understanding of these crucial topics, ensuring you walk away with a solid grasp of the concepts and their real-world applications. The quizzes are designed to challenge your knowledge and give you the confidence to navigate these advanced technologies. What's more, we've prepared great prizes for each quizz, so don't hesitate to join our workshop!
As a special highlight, there will be a live demonstration of the latest Signature Activation Module, certified and compliant with the requirements of eIDAS (the EU regulation on electronic identification and trust services for electronic transactions). This module represents a key innovation in ensuring the secure and authenticated signing of digital transactions, offering robust protection for individuals and businesses alike.
Join us to experience firsthand how these advancements will shape the future of digital security—and get a sneak peek at the latest tools and strategies that will keep you ahead of the curve.
Mandatory equipment: Mobile device with a camera and an internet connection.
Marko Bobinac is leading Thales’s Alliances in the area of Payment and Trusted Services. Through the 13+ years in Thales Marko was working with all Encryption, Key Management and Authentication solutions from Thales CPL is portfolio.
Marko has experience in Customer projects for securing Confidentiality, Integrity, Availability and Accountability with Network Encryption, Payment security solutions, modern PKI infrastructure, efficient Storage&File encryption, DB encryption, Data Anonymization and other encryption based solutions. He is also one of the pillars of Thales’s eIDAS strategy for both Authentication and Hardware Security Modules product lines.
Daniel Danilovski holds a B.Sc. degree in electrical engineering, with nearly 30 years of professional experience and expertise in developing system infrastructure for complex digital transformation solutions and trust services.
Daniel is Manager of Professional Services of Nextsense and trust services expert. His dedication to development of advanced technologies for improvement of organizations’ performance and their digital transformation, resulted in introducing Nextsense’s innovative solutions and products for digital signing and working with e-documents. With Daniel’s significant contribution, Nextsense developed the digital signing portfolio of products and services – Nextsense Signing Suite.
His proven expert capabilities are reflected in numerous, successfully implemented digital signing solutions, digitalization and business processes automation, positioning Daniel as an expert for complete secure solutions for providing e-identification services, authentication and integrity, in compliance with the European regulation eIDAS.

Marko Đuričić
Senior Legal and Data Protection Counsel
at Visage Technologies
Shadow AI & the Illusion of Control: Why AI Governance Fails Without Technical Verification | .lead
AI governance has become one of the main topics for organizations adopting and using AI tools. Companies are introducing internal policies, governance frameworks, approval processes, and risk assessments in an effort to establish control over the use of artificial intelligence.
However, an important question remains: how much of that control is actually real?
This session will explore the phenomenon of Shadow AI, but also the broader question of how much control organizations truly have over the AI systems they use, including those that have been formally approved and integrated into business processes.
Particular attention will be given to AI governance models that often rely on internal policies, approval workflows, and vendor documentation, while offering only limited ability to independently verify how AI systems process data, generate outputs, and evolve over time.
The presentation will discuss the challenges of technical verification of AI systems, reliance on vendor claims, risks associated with AI coding assistants, prompt leakage, and uncontrolled data flows, as well as the gap between security, compliance, and legal functions on one side and the actual use of AI tools within organizations on the other.
Rather than providing a regulatory overview or debating the benefits and risks of AI in general, the session aims to examine how effective AI governance can be when organizations don't independently verify what is actually happening under the hood of the systems they rely on.
At its core, the presentation asks a simple question: if AI governance is not supported by technical visibility and verification, are organizations managing AI risks or merely managing assumptions?
Marko Đuričić is a legal professional with more than a decade of experience in business law, with a particular focus on data protection, artificial intelligence, and technology law. He graduated from the Faculty of Law, University of Zagreb, in 2012.
He currently serves as Senior Legal and Data Protection Counsel at Visage Technologies, a technology company specializing in AI solutions, where he advises on GDPR and EU AI Act compliance, conducts legal risk assessments for AI products, and provides legal support on a broad range of matters affecting a technology company. He has gained hands-on experience with data and the regulatory implications of AI systems through direct involvement in product development and compliance activities. In addition, he operates as an independent consultant through SummIT Lex, providing business advisory services related to the technical implementation of EU regulations in the fields of data protection, artificial intelligence, and information security.
Prior to joining Visage Technologies, he led the in-house legal team at Croatian Post, where he advised on strategic projects, contractual relationships, M&A transactions, and business processes. His previous experience also includes working with several law firms, including Batarelo Dvojković Vuchetich, Knezović & Partners, Gugić, Kovačić & Krivić, and Željko Rački & Associates.

Marko Grbić
Director of Business Development
at LNG Croatia
Critical infrastructure: OT security vs operations | .ops
How to build up cyber security level in critical infrastructure where operations are 24/7/365 and cost of downtime is unmeasurable. Using that same cost of downtime as a push towards increasing cyber security while avoiding any impact on operations.
Graduated from University of Zagreb, Faculty of Electrical Engineering and Computing, obtained a master's degree in electrical engineering and information technology, majoring in automation. More than 10 years of experience in the energy sector with an emphasis on OT infrastructure such as process control systems and safety instrumented systems in industrial plants.

Marko Grbić
Director of Business Development
at LNG Croatia
Airgap in OT - myth or reality? | .ops
What is OT and how has it evolved over the past decade? What is an airgap in theory and has it ever really existed in the real world? The role of the vendors in the (in)security of the OT system. New technologies and security approaches in OT systems.
Graduated from University of Zagreb, Faculty of Electrical Engineering and Computing, obtained a master's degree in electrical engineering and information technology, majoring in automation. More than 10 years of experience in the energy sector with an emphasis on OT infrastructure such as process control systems and safety instrumented systems in industrial plants.

Martin & Valent Sinković
Keynote presentation
Sinković brothers are world and Olympic champions in rowing, as well as world record holders in double sculls. The most successful rowing pair in Croatian history, they dominated in double sculls before bravely switching to coxless pair. As a first pair ever, they were Olympic, world and European champions two different rowing disciplines. With three gold and one silver Olympic medal, they are the most decorated Croatian Summer Olympians in history. Martin and Valent are six-time world champions and seven-time European champions, spanning three different disciplines, quadruple sculls included.

Matija Mandarić
Presales engineer
at Trend Micro
Capture the Flag
Step into the shoes of an Incident Responder for a few hours and learn how they analyze incidents, piece together the puzzle, and defend against existing or future attacks. Additionally, you will see how with the right tools, this job can truly be done in such a short timeframe.
This will be a CTF-style workshop, with the curiosity that it is a defensive CTF, which is not common; typically, you can find Red Team tasks, i.e., offensive tasks, online. Through solving various tasks, participants will familiarize themselves with tactics and techniques that attackers use in targeted attacks, including phishing emails, script usage for system access, and running malicious code in RAM. How to detect, stop, and prevent such attacks.
From a security engineer to presales and consulting, enterprise security architecture and education. Matija has been in security for 15 years, in various roles and various organisations with various responsibilities, from a user through an integrator to a vendor. He likes to joke that it made him jack of all trades but master of none (although the continuation of that saying is very indicative). But hey, as an SF author once wrote, specialisation is for insects?
-
Register for this workshop here.

Matija Mandarić
Presales Engineer
at Trend Micro
Workshop: Capture the Flag
Capture the Flag is a very popular format of blending fun with learning new skills and we are delighted to have an opportunity to offer this as one of our workshops at third DEEP conference. This workshop will introduce you to the functionality of XDR technology and facilitate the acquisition of skills you need to develop to deal with advanced attacks. Each participant should bring own laptop to the workshop. If you are already registered for the conference, you can book your place by an email to [email protected]. If there will be demand, workshop will be repeated on the second day of the conference.
From a security engineer to presales and consulting, enterprise security architecture and education. Matija has been in security for more than a decade, in various roles and various organizations with various responsibilities, from a user through an integrator to a vendor. He likes to joke that it made him jack of all trades but master of none. But hey, as an SF author once wrote, specialization is for insects!

Matija Mandarić
Presales engineer
at Trend Micro
Step into the shoes of an Incident Responder for a few hours and learn how they analyze incidents, piece together the puzzle, and defend against existing or future attacks. Additionally, you will see how with the right tools, this job can truly be done in such a short timeframe.
This will be a CTF-style workshop, with the curiosity that it is a defensive CTF, which is not common; typically, you can find Red Team tasks, i.e., offensive tasks, online. Through solving various tasks, participants will familiarize themselves with tactics and techniques that attackers use in targeted attacks, including phishing emails, script usage for system access, and running malicious code in RAM. How to detect, stop, and prevent such attacks.
From a security engineer to presales and consulting, enterprise security architecture and education. Matija has been in security for almost 15y now, in various roles and various organisations with various responsibilities, from a user through an integrator to a vendor. He likes to joke that it made him jack of all trades but master of none (although the continuation of that saying is very indicative). But hey, as an SF author once wrote, specialisation is for insects?

Matko Radić, moderator
Senior information security consultant
at Diverto
Threat Intelligence and Collaboration - The key to proactive defense
The panel will take place on the October 24th, 14:45 - 16:20, at the Falkensteiner Punta Skala, hotel IADERA, Conference hall: Levant A
The moderator of the panel is Matko Radić, Senior Information Security Consultant at Diverto,
Panel guests:
- Nataša Glavor, CERT
- Josep Estevez, Marlink/Omniaccess
- Fyodor Yarochkin, Trendmicro
- Vanja Švajcer, Cisco Talos

Mikko Hyppönen
Chief Research Officer at WithSecure and Principal Research Advisor
at F-Secure
Keynote presentation
In unlikely case you didn’t hear about this leading global security expert, speaker and author, he works as the Chief Research Officer at WithSecure and as the Principal Research Advisor at F-Secure.
Mr. Hypponen has written on his research for the New York Times, Wired and Scientific American and he appears frequently on international TV. He has lectured at the universities of Stanford, Oxford and Cambridge. He was selected among the 50 most important people on the web by the PC World magazine and was included in the FP Global 100 Thinkers list. Our keynote presenter sits in the advisory boards of t2 and Safeguard Cyber.

MJ Casado
Cyber & Threat Intelligence Lead
at Marlink
From Overwhelmed to Operational: Leveraging CTI to Master Your External Attack Surface | .ops
In an era where digital ecosystems expand beyond traditional perimeters, an organization’s external attack surface has become one of the most critical and exposed components of its cybersecurity posture. This presentation explores how Cyber Threat Intelligence (CTI) can be strategically leveraged to identify, prioritize, and mitigate risks across the external attack surface. By correlating threat actor behaviours, tactics, and infrastructure with exposed assets, CTI provides the contextual awareness needed to transform reactive defence into proactive resilience.
Through real-world examples and case studies, the session will demonstrate how integrating CTI-driven insights into External Attack Surface Management (EASM) enables organizations to continuously discover shadow assets, detect misconfigurations, and reduce exposure to emerging threats. Attendees will gain practical guidance on building an intelligence-led EASM program that enhances visibility, accelerates remediation, and strengthens overall cyber defense posture.
MJ Casado is a Threat Intelligence Analyst with over a decade of experience in cyber threat and security intelligence, including 8+ years focused on maritime environments. She currently leads global threat intelligence operations at Marlink, where she oversees intelligence coordination with the Maritime SOC and IR team to defend a fleet of 1,500+ vessels.
Her background includes leading the CTI unit of a global consulting firm, supporting threat intelligence services across 20+ countries, and developing intelligence-driven defense capabilities for the LNG fleet of a multinational energy company.
Passionate about applied intelligence in cybersecurity, she specializes in translating complex threat data into actionable insights in high-risk, operationally constrained sectors. Her work bridges the gap between strategic intelligence and technical execution in critical infrastructure and maritime domains.

Panel discussion
Incident Response 2.0: Aligning with DORA and NIS 2 Without Losing Agility
Moderator:
Mario Blažević, Marlink Cyber
Guests:
Milan Parat, Hrvatska udruga banaka
Slaven Smojver, Hrvatska narodna banka
Sven Škrgatić, A1 Hrvatska
Cyber incidents are no longer the exception but the everyday reality, as many Croatian organizations that have been targeted by attack groups have experienced over the past year. These events have shown that incidents do not happen “somewhere else”, but to everyone – regardless of sector or size.
In a world where attacks are faster, more complex and increasingly automated, the key difference between organizations that successfully recover and those that do not lies in their readiness and agility.
Artificial intelligence is further changing the dynamics: attackers use it for automation and social engineering, while defense teams apply AI for faster detection and response.
The DORA and NIS 2 regulations set strict requirements for incident management – with deadlines of 24 to 72 hours, defined roles and crisis communication. However, the real challenge is not just compliance, but the ability to maintain speed and coordination within these frameworks.
The panel brings together representatives from regulators, the financial sector, and the telecom industry to discuss how to meet regulatory requirements without losing agility and how to develop a culture of resilience based on people, processes, and technology.

Rob van Os
Founder
at Argos Cyber Security Assessment
SOC-CMM – Maximize your SOCs growth potential
The SOC-CMM is a free model and tool to measure capability and maturity in Security Operations Centers (SOCs). Since its original release in 2016, it has become a defacto open standard for SOC maturity measurement.
The SOC-CMM allows SOCs to gain insight into their strengths and weaknesses across 5 domains and use this information to strengthen their cyber defenses, mature their security operations and demonstrate growth.
In this presentation, Rob, the author of the SOC-CMM model and tooling, will explain the SOC-CMM model and the accompanying assessment tool and how to practically apply it to SOCs. Additionally, the usage of the SOC-CMM for purposes of target operating modelling and defining a strategic direction for the SOC is explained.
Rob van Os, MSc. is a strategic SOC advisor, who has over a decade of practical experience in security operations. Rob has held several positions in SOCs, from analyst to engineer, from incident responder to SOC manager. Currently, Rob helps SOCs address their strategic challenges, from SOC modernisation and transformation to defining and achieving strategic direction.
Rob has obtained a Bachelor's degree in Computer Science from Amsterdam University of Applied Sciences in 2009 and a Master's degree in Information Security from Luleå University of Technology in 2016. Rob is the founder of SOC-CMM and Argos Cyber Security Assessment, helping cyber defence teams achieve their growth and maturity goals. Rob is also a trainer for Security Academy and SECO Institute, author of security articles and conference speaker

Robert Kopal
Chairman of the Board
at EFFECTUS University of Applied Sciences
The role of Artificial Intelligence in Cybersecurity | .lead
There are lots of benefits of using AI and automation in cybersecurity: protecting data across hybrid cloud environments; generating more accurate and prioritized threats; balancing user access needs and security etc. Also, adopting AI-powered automation can help cybersecurity teams drive improved insights, productivity, and economies of scale.
It has been suggested that current operational reality demands a new approach. And this is true.
Especially when you look the data (IBM report, AI and automation for cybersecurity). For example, majority of executives—globally and across industries—are adopting or are considering adoption of AI as a security tool. 64% of executives have implemented AI for security capabilities and 29% are evaluating implementation.
They report AI applications have delivered significant positive impacts on their security outcomes. As for the cybersecurity these include the ability to triage Tier 1 threats more effectively, detect zero-day attacks and threats, and reduce false positives and noise that require human analyst inspection.
Top-performing AI Adopters illustrate the potential for AI to transform cyber defense operations. Their use of AI has helped reinforce network security by monitoring 95% of network communications and 90% of endpoint devices for malicious activity and vulnerabilities. They estimate that AI is helping them detect threats 30% faster. They are also significantly improving response times to incidents and the time to investigate. And their return on security investment (ROSI) has jumped 40% as well.
To summarize in one sentence: only 7% of executives are not considering the use of AI for cybersecurity.
But, is this approach of using AI and automation for cybersecurity without challenges? And, how to implement such approach? What are the benefits but also risks? Are there other approaches?
Robert Kopal, Ph.D., Associate Professor; Senior Research Associate; Tenured University College Professor; Chairman of the Board at EFFECTUS University of Applied Sciences.
Professional and scientific experience: Special Advisor to the Prime Minister for National Security; Acting minister & State Secretary at Ministry of the Interior; Chief Intelligence Analyst at Ministry of the Interior and Senior Manager at the Security and Intelligence Agency; 3x Dean Effectus University College for Law and Finance; Vice Dean for R&D at Algebra University College and Head of the professional master study programs of Digital Marketing and Data Science; Vice Dean for Academic Affairs at Libertas International University; Lecturer and visiting lecturer at numerous university colleges in Croatia and abroad and at CROMA EduCare Programme (Croatian Managers and Entrepreneurs Association); R&D Executive Director at Tokić; Advisor of the Board at IN2 Group for R&D/Science Advisor; Chief Science Officer at IN2data; Author of 13 books published in Croatia and abroad (Intelligence Analysis; Game Theory, Competitive/Business Intelligence Analysis Techniques, Analytical Management, Economic Analysis of International Terrorism, etc.); Author of a number of chapters in books and of about 70+ professional and scientific papers in Croatia and abroad; Head of, and lecturer at over a hundred business and analytical workshops in Croatia and abroad (trained intelligence & law enforcement officers from 11 countries); Head of PIU & Key Expert: “CARDS Twinning project: Criminal Intelligence System, Phase 1&2” te Project Liaison Officer na UNODC (United Nations Office on Drugs and Crime) projektu “Strengthening of Capacities for Collection and Analysis of Criminal Intelligence in South-eastern Europe”; 2 UNODC commendations; Designed several specialized IT systems; certified intelligence analysis techniques and intelligence analysis software trainer; Member of IALEIA (International Association of Law Enforcement Intelligence Analysts) and BDVA (Big Data Value Association); Editor-in-Chief of the International Journal of Digital Technology and Economy and member of the editorial board of the International Journal of Economics &; Management Sciences; Speaker at various national and international conferences; Participant and head of multiple national and international analytical projects; Member of the Agency for Science and Higher Education Commission for Social Sciences; Member of the National Council for the Development of Human Potential; Member of National Cyber Security Council; Member of the Croatian national team - European Big Data Hackathon 2017, which won the 1st prize, etc.; Penultimate book Analytical management has won 2 awards and the last book is Intelligence Analysis; Karate 2nd Dan black belt.

Robert Kopal and Darija Korkut
Leading security specialists
at Academic community
Applying ACH (Analysis of Competing Hypotheses) in Cybersecurity
Workshop description: The rationale for the workshop is as follows: (1) security expert's forecasting and predictions are too often wrong – and too often experts are making fallacies or mistaken inferences and succumb to faulty reasoning.; (2) long-term study has shown that too much knowledge can have an adverse effect on the accuracy of prediction (for example the expert forecast accuracy in foreign affairs is about 35%); (3) experts are human and "to err is human" – and being expert in certain field is not the same as being a critical thinker (4) most of the intelligence failures (by experts) have common denominators: extinct by instinct; expert blindness; overestimation; underestimation; over-confidence; subordination of intelligence to policy; lack of communication; unavailability of information; received opinion; mirror-imaging; complacency/smugness; failure to connect the dots, etc.
All these issues can be solved with the appropriate intelligence analysis approach integrated into cybersecurity.
But there are some challenges regarding cyber threat intelligence (CTI): 85% of security professionals believe their CTI program requires too many manual processes; 82% of security professionals agree that CTI programs are often treated as academic exercises; 72% of security professionals believe that it is hard to sort through CTI noise to find what’s relevant for their organizations; 71% of security professionals say it is difficult for their organizations to measure ROI on its CTI program; 63% of security professionals say that their organization doesn’t have the right staff or skills to manage an appropriate CTI program (Research Report: Cyber-threat Intelligence (CTI) Programs: Ubiquitous and Immature).
Another recent survey of 1,350 IT and business leaders, representing organizations with 1,000 or more employees across 13 countries (released by Mandiant) uncovers additional CTI challenges: 79% of the surveyed leaders said that “the majority of the time, they make decisions without adversary insights" because "organizations feel they have too much threat intelligence information coming in through their feeds — and they aren’t able to sift through it effectively enough to have it influence their decisions". Furthermore, 47% of surveyed leaders reported that “applying threat intelligence throughout the security organization” is among their biggest challenges.
The aim of the workshop is to explore benefits of applying intelligence analysis techniques in various cyber scenarios, including cyber attribution challenges, to help organizations gain a complete picture of an attack and enhance their cybersecurity strategy for the future.
Analysis of competing hypothesis is one such technique. It’s a structured analytic technique commonly used in cyber threat intelligence. As its name indicates, it is used to determine the most likely hypothesis among several, simultaneously comparing multiple hypotheses against a given range of evidence.
It can be effectively used in the analysis phase of the cyber threat intelligence cycle to bring the clarity and objectivity, making it easier to analyze complex situations.
THE MOST DILLIGENT PARTICIPANT WILL BE AWARDED THE INTELLIGENCE ANALYSIS BOOK AUTHORED BY KOPAL AND KORKUT!
If you are already registered for the conference, you can book your place by an email to [email protected].
Duration: 90 minutes
Trainers: Associate Professor Robert Kopal, PhD; Darija Korkut
Trainers’ bio:
Robert Kopal, Ph.D., Associate Professor; Senior Research Associate; Tenured University College Professor; Chairman of the Board at EFFECTUS University of Applied Sciences.
Professional and scientific experience: Special Advisor to the Prime Minister for National Security; Acting minister & State Secretary at Ministry of the Interior; Chief Intelligence Analyst at Ministry of the Interior and Senior Manager at the Security and Intelligence Agency; 3x Dean Effectus University College for Law and Finance; Vice Dean for R&D at Algebra University College and Head of the professional master study programs of Digital Marketing and Data Science; Vice Dean for Academic Affairs at Libertas International University; Lecturer and visiting lecturer at numerous university colleges in Croatia and abroad and at CROMA EduCare Programme (Croatian Managers and Entrepreneurs Association); R&D Executive Director at Tokić; Advisor of the Board at IN2 Group for R&D/Science Advisor; Chief Science Officer at IN2data; Author of 13 books published in Croatia and abroad (Intelligence Analysis; Game Theory, Competitive/Business Intelligence Analysis Techniques, Analytical Management, Economic Analysis of International Terrorism, etc.); Author of a number of chapters in books and of about 70+ professional and scientific papers in Croatia and abroad; Head of, and lecturer at over a hundred business and analytical workshops in Croatia and abroad (trained intelligence & law enforcement officers from 11 countries); Head of PIU & Key Expert: “CARDS Twinning project: Criminal Intelligence System, Phase 1&2” te Project Liaison Officer na UNODC (United Nations Office on Drugs and Crime) projektu “Strengthening of Capacities for Collection and Analysis of Criminal Intelligence in South-eastern Europe”; 2 UNODC commendations; Designed several specialized IT systems; certified intelligence analysis techniques and intelligence analysis software trainer; Member of IALEIA (International Association of Law Enforcement Intelligence Analysts) and BDVA (Big Data Value Association); Editor-in-Chief of the International Journal of Digital Technology and Economy and member of the editorial board of the International Journal of Economics &; Management Sciences; Speaker at various national and international conferences; Participant and head of multiple national and international analytical projects; Member of the Agency for Science and Higher Education Commission for Social Sciences; Member of the National Council for the Development of Human Potential; Member of National Cyber Security Council; Member of the Croatian national team - European Big Data Hackathon 2017, which won the 1st prize, etc.; Penultimate book Analytical management has won 2 awards and the last book is Intelligence Analysis; Karate 2nd Dan black belt.
Darija Korkut, Senior Lecturer, doctoral student of Information Society at the Faculty of Information Studies in Novo Mesto, Slovenia. She was working at the Ministry of Foreign and European Affairs, as an information and analysis officer, and as a diplomat at the Croatian Embassy in Dublin. In her 10-year experience at the Security Intelligence Agency she was working on analytical education and training, and the development of innovative technological solutions. In January 2019, she joined University College Effectus, where she teaches Analytical Management, Critical Thinking, Behavioral Economics, Psychology of Decision Making, and Decision Making under Risk and Uncertainty. Darija has co-authored eight books, and a number of professional and scientific papers on analytical management, game theory, social network analysis, creativity, and behavioral economics. Her latest book, co-authored with Robert Kopal, covers the area of intelligence analysis in both, corporate and security intelligence application. She has participated in numerous domestic and international courses, seminars, and conferences in the field of international relations and diplomacy, and various analytical courses and workshops (NATO, US EUCOM, FBI among other), and as a lecturer at many of those. She owns international certificates in structured analytical techniques and critical thinking. Areas of interest: creativity and innovation, critical thinking, problem solving, behavioral economics, social network analysis, game theory, intelligence analysis, analytical management.

Robert Petrunić
Security consultant
at Eduron IS
NTLM is dead, long live the Kerberos | .tech
Most companies worldwide use some kind of LDAP (Lightweight Directory Access Protocol), and many of these use Microsoft AD and/or Microsoft Entra AD, because, let's be honest, it's the mostly used LDAP in the world within corporate environments. During the penetration testing engagements, author of this lecture identified many AD misconfigurations which led to partial or in most of the cases complete AD takeover, which is troublesome, to say the least.
There are a lot of attack vectors available for attacking (usually) misconfigured AD, and in this lecture, we will try to discuss some of these, specifically the ones the author usually sees and compromise in PT engagements. The lecture will be demo based, instead of theory based, because the lecture time is limited and it is impossible to cover even 10% of usual attacks in theory, and even less in demo. We will dream big and try to demonstrate and explain as much as possible of the following attacks: Kerberos AS-REQ user enumeration, to identify AD accounts in a really fast and safe way, then AS-REP and kerberoasting (these two are quick, and a good demo for warming-up), followed by DCSync attacks. We will unfortunately have to skip the golden (ticket, certificate, and SAML) attacks, including the Silver ticket attacks, as the time is an issue, and continue with DCSync and (if time permits) unconstrained delegation attacks. The rest of the demo will be devoted to AD CS (Active Directory Certification Services) attacks, and we will cover as much as possible of the E1-E11 elevation paths to domain admin accounts.
The sole purpose of this lecture is for the participants to "feel" how vulnerable they environments could be out of the box and if misconfigured, and to understand the possible implications. Demonstrated attacks show NTLM and Kerberos vulnerabilities.
Robert works as a senior information security consultant in Eduron IS and he’s a lecturer in most successful Croatian private college Algebra. He’s Microsoft certified trainer since 2002, EC-Council certified trainer since 2008 and ISC2 certified trainer since 2014. Since 2004. Robert is working on programs related to ethical hacking and IT security awareness for systems administrators, developers and IT security consultant.

Robert Petrunić
Senior information security consultant
at Eduron IS
DeeP or just the root-cause Pentest? | .tech
Penetration testing is usually done in such a way as to identify the vulnerability (root cause) and to stop there without full penetration. Then, the process is repeated until as many vulnerabilities are identified as possible. This is a good approach because it allows the penetration tester to identify as many vulnerabilities as possible in as short time as possible. To put it in the business language, we talk about cost-benefit, as this approach gives better ROI (Return on Investment). However, this approach might have some drawbacks because we are left in the dark about what might have happened before we identified this vulnerability and what the attacker might have access to if this vulnerability had already been compromised in the past. For instance, what if the attacker gained access to a web server through the web application vulnerability and then scanned the network behind the web server where other servers and services are accessible, usually not accessible directly from the Internet? It might allow the attacker horizontal and possibly vertical movement through the systems behind, systems not intended to be exposed to the Internet atoll!
This lecture will discuss some real-world examples of how the full penetration (going as deep as possible after initial compromise by hacking not only the compromised application, service, or OS but also everything else that is hackable) identified additional misconfigurations and vulnerabilities which could lead to an entire company and supply chain compromise just because one service exposed to the Internet was hacked. We will use some interesting case studies (anonymized, of course) to show the importance of full penetration. This led to a computer forensics project because Pentest identified the possibility of system compromise or even live attackers in the system. Some case studies covered: Atlassian Confluence, Magento, AD, managing app for 10 000+ IoT devices and vCenter server appliance, ...
Robert is a senior information security consultant at Eduron IS, a company dedicated to IT security education, penetration testing, and computer forensics. He also works as a lecturer in the most successful Croatian private college, Algebra - University College for Applied Computer Engineering, where he has designed several computer security and forensics courses.
Robert has been a Microsoft certified trainer since 2002, an EC-Council certified trainer since 2008, and an ISC2 accredited trainer since 2014. He has worked mainly in the security field starting in 2004, and Microsoft acknowledged this in 2008, assigning him Microsoft's most valuable professional recognition for nine years in a row.
For the last twenty years, Robert has worked on programs related to ethical hacking and IT security awareness for systems administrators, developers, and IT security consultants. He is also often a lecturer at regional IT conferences.

Robert Petrunić
Security consultant
at Eduron IS
Devil vs. Smurf, or Devil + Smurf? | .tech
Red teaming is nothing new. It is a concept much, much, much older than this conference.
The problem is that red teaming is not widely implemented and used in the companies.
There are many benefits to it though, one being the exponential growth of the blue team capabilities and network/server/application security.
So, why don't you have the red team in your company yet?
This lecture with shortly define red/blue/purple/orange/green/yellow teaming, and stay focused on the red teaming benefits, and continue with explaining on how the red teaming relates with DORA Act and NISv2 Directive.
We will also suggest the red teaming implementation paths, supply recommended training sessions and certification needed for the team members. You will get all you need to start your red team and to pitch the idea to your management to get the founding.
What are you waiting for? CU
Robert works as a senior information security consultant in Eduron IS and he’s a lecturer in most successful Croatian private college Algebra. He’s Microsoft certified trainer since 2002, EC-Council certified trainer since 2008 and ISC2 certified trainer since 2014. Since 2004. Robert is working on programs related to ethical hacking and IT security awareness for systems administrators, developers and IT security consultant

Rok Likar
Presales Engineer
at MBCOM Technologies
Demystifying API Management | .tech
Unlock the secrets of effective API management with our presentation, "Demystifying API Management" Explore the robust functionalities of Layer7 as we share regional use cases, revealing practical insights and success stories. Join us on this journey to clarity, where we simplify the complexities of API management and provide actionable strategies for success.
Rok is presales Engineer at MBCOM Technologies, specializing in tailored software solutions for Broadcom's Enterprise Software Division. Over a decade of experience, with a focus on successful pre-sales engagements and practical IT solutions. Previous roles include expertise in Broadcom Service Management, other CA solutions, and system administration. Committed to driving efficiency and excellence in IT.

Saša Zdjelar
Chief Trust Officer
at ReversingLabs
The World Runs On Open Source But Your Company Doesn't: Unmasking Commercial Software Risks | .lead
We hear the phrase "the world runs on open source" often and while it's true that most software contains a lot of open source, enterprises run on commercial software. Business processes and value chains depend on commercial software due to the need for support, patching, continued investments for enterprise use cases, etc., meanwhile software supply chain attacks have risen 1300% in the past few years. In this talk we're going to discuss the current capabilities available to CISOs to manage software supply chain risks, evolving regulatory and personal liability expectations and what security leaders can do to protect their company.
Saša is an Operating Partner at Crosspoint Capital and the Chief Trust Officer (CTrO) at ReversingLabs with ~20 years of Fortune 10 global executive leadership experience. His CTrO scope includes leadership, oversight and governance of the CISO/CSO function, including product security, as well as partnering with other leaders on corporate and product strategy, strategic partnerships and research, and customer and technology advisory boards, including sponsoring the ReversingLabs CISO Council.
Prior to ReversingLabs and Crosspoint Capital, Saša served as the Senior Vice President of Security at Salesforce, where he led a global organization encompassing enterprise security, product security, offensive security, security engineering/automation, bug bounty programs, technical product/program/project management, and mergers & acquisitions. He was also the executive sponsor for strategic corporate security initiatives, such as Zero Trust.
Prior to his tenure at Salesforce, Saša spent nearly two decades at ExxonMobil, holding various positions focusing on strategy, enterprise security & architecture, software engineering, ERP systems design/integration, program and product management, planning & stewardship, compute and hosting platforms, and digital/cyber resilience.
Saša is an active participant and founding member of several CISO leadership communities. He is also a member of the Forbes Technology Council, Member of the Board at the National Technology Security Coalition (NTSC), a Fellow at the Cyber Readiness Institute (CRI), a Fellow at the Center for Global Enterprise (CGE), a member of the BlackHat CISO Summit Advisory Board and BlackHat Content Review Board, and engages in organizations such as Infragard, ISACA, and ISSA. His insights have been published in various industry publications, and he has spoken at numerous industry conferences and universities.
Saša holds a Bachelor's degree in Management and a Master's degree in Decision Science from the University of Florida.

Sebastian Mazurczyk
Senior Sales Engineer
at TXOne Networks Europe
Native Tools (or ‘Toys’) to Protect Your OT: Challenges, How to Overcome Them and a Live Demo | .tech
This presentation will address the key challenges associated with implementing protection systems for industrial networks and the potential impact of attacks on such environments. Selecting appropriate security tools tailored to the specific nature of OT environments is crucial to ensuring the safety and continuity of industrial processes.
During the session, I will discuss several tools and demonstrate one of the dedicated security solutions designed for OT environments, showcasing how it can be efficiently deployed and what capabilities it provides for protecting industrial networks.
Participants will also learn about solutions that mitigate the risks associated with the use of portable storage media — an aspect emphasized in NIST guidelines.
With over 18 years of experience in the IT industry, primarily focused on security systems. He has built extensive experience working in the distribution market as a presales and postsales engineer.
For the past 3 years, he has concentrated on security solutions dedicated to OT, starting from monitoring and vulnerability detection solutions to active protection.

Silvio Plehati and Jana Žiljak Gršić
Lecturer / Assoc. Professor and Dean
at Zagreb University of Applied Sciences
Multi-factor INFRAREDESIGN® authentication in the VIS/NIR spectrum | .ops
New application for multi-factor user authentication in two spectral areas is created. Application use a method of separating information using INFRAREDESIGN® technology. The application employs two cameras in two spectral areas: VIS (visible) 400-750 nm and NIR (near-infrared) at 1000 nm, and is capable of detecting human faces and QR codes. One of the key features of the application is the verification of user authenticity through multiple factors simultaneously. Detection of faces, QR codes, and other markers provides an additional level of security, while simultaneous authenticity checks in both spectral areas ensure that information separation is correctly performed for the same individual, object, or marker. Separation is accomplished using INFRAREDESIGN® technology, and this approach enhances the security of the authentication system as users must go through multiple verification steps to gain access. The application also allows for capturing images of "regions of interest" in both spectral areas for further deep learning or analysis. Multi-factor authentication takes place simultaneously in real-time in both spectral areas using multiple detection algorithms. During this presentation the spotlight is on multiple examples INFRAREDESIGN® secured items for dual-spectrum authentication using two cameras. This will encompass not only the detection process but also the real-time visual representation of authentication, leading to access approval.
Prof. dr. sc. Jana Žiljak Gršić, scientific adviser:
In 1996, she graduated from the Design Study at the Faculty of Architecture, University of Zagreb, and in 2007, she received her doctorate from the Faculty of Graphic Arts, University of Zagreb. For the innovation Infraredizajn, she received the national science award in 2010 for scientific discovery and the Nikola Tesla Award for the best Croatian innovation in 2012, as well as more than 100 prestigious world awards, which she shares equally with her colleagues.
She has been the dean of the Zagreb University of Applied Sciences since 2021, where she has been employed since 2002. She teaches at the North University on graduate and doctoral studies as her secondary employment. As an external associate, she teaches at the doctoral studies of the Faculty of Graphic Arts, University of Zagreb, and at the doctoral studies of Alma Mater Europaea in Maribor.
She is the secretary of the graphic engineering department of the Croatian Academy of Engineering for the term 2022 - 2026. She is the founder and member of the editorial board of the Polytechnic & Design journal published by the Zagreb University of Applied Sciences. She is the head and editor of the collection of the professional-scientific conference Printing and Design, which is held under the sponsorship of the Croatian Academy of Engineering. She is a member of several expert councils and expert commissions and a regular member of the Croatian Designers Association.
She is a permanent court expert witness for graphic technology, design, manuscripts, documents, securities, money, pictures, credit cards, and other cards.
She participated in ten scientific, professional and technological projects approved by the Ministry of Science and Education and the Croatian Science Foundation. Together with her collaborators, she has registered four patents at the State Intellectual Property Office. She actively participated in the development of the curriculum of the Informatics and Computing Department of the Zagreb University of Applied Sciences, and she designed the program of the Informatics Design major at the professional and graduate studies in Informatics. She introduced numerous courses in the fields of design, web design, 3D modeling, visual communication, security graphics and innovation, which she teaches. She participated in the launch of the new study program Information Security and Digital Forensics at Zagreb University of Applied Sciences and in the internationalization of the said study program. In two terms, she was the head of the professional study of informatics and in two terms the head of the Informatics and Computing Department of Zagreb University of Applied Sciences.
She is the author of the textbook Safety graphics published by the Zagreb University of Applied Sciences and published numerous professional works, including those in collaboration with students of the Zagreb University of Applied Sciences (CROSBI Profile: 34737, MBZ: 264064). She is the author of many visual identities, posters and packaging for a wide range of customers. She has participated in solo exhibitions and group international and domestic juried exhibitions in the field of design and innovation. She organized exhibitions of student works in recognized galleries of the City of Zagreb and encouraged the application of students and teachers to innovation exhibitions in the country and around the world. She led the project in which IT design students participated named Techno Past Techno Future: European Researchers' Night (TPTF_ERN) Marie S. Curie European Research Night, EU Framework Program for Research and Innovation in 2018 and 2019.
Silvio Plehati, MEng(IT), MSc(Graph.Techn.), Lecturer at Zagreb University of Applied Sciences:
In 2003, Silvio Plehati completed his undergraduate studies in Information Technology at the Zagreb University of Applied Sciences. In 2010, he completed his graduate studies in Information Technology at the same faculty. In 2023, he completed the study of Graphic Technology at the Faculty of Graphic Arts, University of Zagreb. That same year, at the Faculty of Graphic Arts, he was awarded the Dean's Award for publishing two scientific papers of category A (Q1/Q2) in 2022/2023. In 2023, he enrolled in a doctoral program at the same faculty. Since 2003, he has been continuously working in the field, establishing a bridge between computer science and graphic technology. He has co-authored professional and scientific papers in the fields of graphic engineering and graphic programming, focusing on the design of graphic protections through programming. Since 2021, he has been employed at the Zagreb University of Applied Sciences. He was appointed as an assistant in 2021 and promoted to lecturer in 2023. He teaches courses in software engineering in open systems, object-oriented programming, and advanced programming techniques. His areas of interest include C languages, graphic programming languages, 2D and 3D graphics, 3D printing, micro (embedded) electronics, and sensors. He actively participates in conferences related to graphic engineering, graphic programming, and computer science.
Stipe Božić
Kako do vrha
In Croatia, Stipe Božić needs no introduction. A legendary mountaineer, man who conquered Seven Summits and climbed Mount Everest twice, he has seen the most remote and unwelcoming corners of the world – and told the story about it in his unique way. After he directed more than 60 documentary films and took thousands of photos, he will show and tell his story to DEEP attendees as the keynote presenter for 2025.

Stjepan Groš
Associate Professor
at University of Zagreb, Faculty of Electrical Engineering and Computing
Cybersecurity Education at FER: Information, Opportunities, and Possibilities for Companies and Government Institutions | .lead
The purpose of this lecture is to introduce companies and government institutions to cybersecurity education at the Faculty of Electrical Engineering and Computing, University of Zagreb (FER), provide insight into students' perspectives on cybersecurity in general, and offer guidelines on how companies and government institutions can get involved in the entire process. In this context, we will explain how cybersecurity education is structured and list the courses at FER across all levels of study. We will also present the results of surveys that we regularly conduct in the course Computer Systems Security (Hrv.Sigurnost računalnih sustava (SRS)) before the start of the course and after all students have completed it. The SRS course is an introductory course on security that all computer science students take in the 6th semester of the undergraduate program, approximately 500 students annually. These surveys provide insight into how familiar students are with cybersecurity in everyday life, how the course changes their perception of security, and what their plans and requirements are in terms of employment, particularly employment in the field of cybersecurity.
Stjepan Groš is an Associate Professor at the University of Zagreb, Faculty of Electrical Engineering and Computing. His research and professional interests lie in the fields of information and cybersecurity, as well as in the application of advanced methods to solve problems in these areas, where he has published numerous scientific papers. Stjepan Groš has led or participated in several EU-funded cybersecurity projects and maintains strong collaboration with various companies and government institutions in Croatia. Since 2014, he has been the head of the Laboratory for Information Security and Privacy, part of the FER’s Center for Artificial Intelligence. He is also the chair of the Information Systems Security scientific conference at the MIPRO convention. Additionally, he serves as a member of the Management Board of the Croatian Defense Industry Competitiveness Cluster. He is a member of the committee for the postgraduate specialist study in Information Security at FER. Stjepan Groš contributed to the development of the National Cybersecurity Strategy of the Republic of Croatia and worked on the Smart Specialization Strategy of the Republic of Croatia 2014-2020 in the area of cybersecurity. He has participated as a panelist or speaker in numerous roundtables and professional conferences related to cybersecurity, information security, research, and development.

Stjepan Groš, moderator
Laboratory for Information Security and Privacy
at FER
Roundtable: Preparations for the alignment with the transposed NIS2 directive | .lead
Recently, new EU NIS2 directive was in focus as the proposed transposition law was open for public consultation this summer. Since the proposal of new Cybersecurity law has entered Parliament procedure, it is time to start thinking about compliance and preparing for the alignment process. Thus, the topic of the roundtable is the preparation for alignment with the new Cybersecurity Law (Zakon o kibernetičkoj sigurnosti). We hope to initiate discussions about this important step and to help everyone to start, at least thinking, about this not so small endeavor that is in front of us.
Some of the questions we plan to tackle on this roundtable are:
What are the prerequisites for starting the compliance process?
Who should be responsible for ensuring compliance within organizations?
How much time do we have, i.e. what is the expected timeline?
What should be included in the necessary budget?
What can be done right now, even without the regulation fully in place?
Can compliance be achieved in incremental steps?
What can be expected from companies that offer compliance services; what do companies expect from their clients; what companies cannot do and clients must do themselves.
Join us at this roundtable and share with us your questions and views regarding this important topic.
Moderator:
Stjepan Groš, Laboratory for Information Security and Privacy @FER
Panelists:
Aleksandar Klaić, Cyber Security Centre @SOA
Mario Kozina, IT Supervisor @HNB
Ana Balaško, Telecommunications and Information security coordinator @HEP ODS
Marko Grbić, Director of Business Development @LNG Croatia
Dario Rajn, CISO @Podravka
Ivan Kalinić, Senior security consultant @Diverto

Tena Velki
Full Professor of Psychology
at Faculty of Education, J.J. Strossmayer University of Osijek
Reptilian Brain Exploited: The Evolutionary Bug in Cybersecurity | .lead
At the core of successful cyberattacks are not only technical vulnerabilities, but also psychological weaknesses of users. Phishing attacks exploit basic emotional and cognitive patterns, such as fear, greed, urgency, and curiosity, which reduce critical thinking. The concept of the “reptilian brain”—primitive neural structures responsible for survival and rapid reactions—explains why users often act impulsively before rationally evaluating potential threats. With AI, these attacks are evolving into smarter forms like vishing and smishing, making the human brain the biggest zero-day vulnerability. Hackers deliberately leverage decision-making heuristics and psychological shortcuts, such as authority, reciprocity, and urgency, to trigger automatic behaviors and divert attention from rational analysis.
True defense requires both technology and psychological resilience: training, awareness, and a culture of “think before you click.” Understanding these mechanisms enables a more comprehensive defense approach, with practical implications for user education, system design, and organizational security culture.
This presentation aims to demonstrate how integrating insights from psychology and cognitive science with technical cybersecurity measures enables a more comprehensive defense approach, emphasizing practical implications for user training, system design, and organizational security culture.
Dr. Tena Velki is a Full Professor of Psychology at the Faculty of Education, J.J. Strossmayer University of Osijek. Her primary areas of expertise are developmental psychology, with a focus on behavioral disorders, and for the last 10 years information security and data privacy.
Dr. Velki is an external collaborator at the Faculty of Electrical Engineering, Computing and Information Technologies and the Faculty of Humanities and Social Sciences in Osijek. She is an active member of several professional organizations, including the Croatian Psychological Association (HPD), the Croatian Psychological Chamber (HPK), and is President of the Osijek Psychological Society (DPO). Additionally, she is a member of the Croatian Association for Behavioral and Cognitive Therapies (HUBIKOT) and the European Federation of Psychologists' Associations (EFPA). In 2017, she received recognition from the Croatian Psychological Association for her significant contribution to the "Psychology Week in Croatia." For her outstanding contribution to the development and promotion of Croatian psychology, she was awarded the "Marulić: Fiat Psychologia" award by the Croatian Psychological Association in 2018. In 2019, she received the Best Published Scientific Paper Award from the Faculty of Philosophy in Novi Sad and the journal Applied Psychology.
To date, she has published over 70 scientific papers and 10 books, including a university textbook on information security (Velki, T. & Šolić, K. (Eds.) (2019). Challenges of the Digital World. Osijek: Faculty of Education, J.J. Strossmayer University of Osijek). Her most significant contribution in the field of information security and data privacy is the creation of “Users’ Information Security Awareness Questionnaire” (UISAQ, Velki & Šolić, 2014), one of the first in the world to test this problematic.

Tena Velki
Full Professor of Psychology
at Faculty of Education, J.J. Strossmayer University of Osijek
Psychological Aspects of Online Risky Behavior: Implications for Data Security and Privacy | .lead
The main goal of presentation is to explore the topic of online risky behavior through a psychological lens, focusing on the interactions between users and information-communication technologies. With the increasing digitalization of everyday life, individuals face growing threats to data security and privacy, often stemming from risky behaviors such as oversharing personal information, engaging with unverified sources, or neglecting cyber hygiene practices. This presentation will discuss the psychological aspects that contribute to these behaviors, including cognitive biases (such as educational paradox), stress (i.e. lower level of inhibition), and social influences (including peer pressure). The results of the research on online risky behavior among different age groups of computer users in Croatia will also be presented. Additionally, it will highlight strategies for promoting safer online practices and improving awareness among different user groups. This includes fostering a culture of awareness and education among users, tailored to different demographic groups, such as children, adolescents, and adults. By understanding the psychological factors behind online risky behavior, we can better protect users and create a safer digital environment.
KEY WORDS: online risky behavior, psychological aspects, information-communication technology users, data security, data privacy
Dr. Tena Velki is a Full Professor of Psychology at the Faculty of Education, J.J. Strossmayer University of Osijek. Her primary areas of expertise are developmental psychology, with a focus on behavioral disorders, and for the last 10 years information security and data privacy.
Dr. Velki is an external collaborator at the Faculty of Electrical Engineering, Computing and Information Technologies and the Faculty of Humanities and Social Sciences in Osijek. She is an active member of several professional organizations, including the Croatian Psychological Association (HPD), the Croatian Psychological Chamber (HPK), and is President of the Osijek Psychological Society (DPO). Additionally, she is a member of the Croatian Association for Behavioral and Cognitive Therapies (HUBIKOT) and the European Federation of Psychologists' Associations (EFPA). In 2017, she received recognition from the Croatian Psychological Association for her significant contribution to the "Psychology Week in Croatia." For her outstanding contribution to the development and promotion of Croatian psychology, she was awarded the "Marulić: Fiat Psychologia" award by the Croatian Psychological Association in 2018. In 2019, she received the Best Published Scientific Paper Award from the Faculty of Philosophy in Novi Sad and the journal Applied Psychology.
To date, she has published over 70 scientific papers and 10 books, including a university textbook on information security (Velki, T. & Šolić, K. (Eds.) (2019). Challenges of the Digital World. Osijek: Faculty of Education, J.J. Strossmayer University of Osijek). Her most significant contribution in the field of information security and data privacy is the creation of “Users’ Information Security Awareness Questionnaire” (UISAQ, Velki & Šolić, 2014), one of the first in the world to test this problematic.

Thomas Roccia
Threat Researcher
Keynote presentation
Thomas Roccia (@fr0gger_) is a Threat Researcher with over a decade of frontline experience. He has handled major cyberattacks, led critical investigations, and spoken at leading security conferences worldwide. He previously worked at Microsoft and McAfee, where he focused on AI security research, incident response, and threat intelligence.
He is the Founder of Security Break, working at the frontier of AI agents and threat intelligence.
Thomas has created multiple open source projects and published extensive research on AI, agentic workflows, and threat intelligence. His work focuses on shaping AI threat intelligence and building practical systems for security teams.
As an early adopter of generative AI for threat intelligence, he has built applications and developed advanced training delivered at Black Hat.
In 2023, he published Visual Threat Intelligence, an international bestseller and Bronze Foreword INDIES Award winner. His work has been featured in media worldwide.
Tihomir Maček, Marin Jaram and Marin Vidaković
| .ops
Tomasz Joniak and Mareike Mett
| .lead

Tomasz Joniak and Mareike Mett
Sr. Solution Engineer / Channel Sales Engineer
at Delinea
Rise above the Noise: Zero Trust Privilege Policy to End User Security | .lead
- What is the current status of Identities/Privileges in today’s Market
- How do compliance and regulations affect the adaption from manual process to PAM
- Can we really control all access of every person
- Does MFA actually work?
- How does Delinea see the PAM landscape?
Tomasz is a Sr. Solution Engineer at Delinea, focusing on securing privileged accounts across the landscape of technology; born in Poland, grew up in Chicago & now, after 30+ years, relocated back to Poland for his next adventure.
Tomasz has extensive 18+ years of working for major IT partners such as WWT, Insight Global, and LaSalle Solutions (now Trace3) as a Security Engineer; relocating to Poland, Tomasz joined Cisco Systems as Sr Security Consulting Engineer and TME, where he focused on ISE and Firepower products part of Product Management.
With his experience, Tomasz joined Delinea to identify and evaluate complex business and technology risks, internal controls that mitigate risks, and related opportunities for internal control improvement utilizing the Mature PAM model to meet today’s IT complexities, as proven by the increase in cyberattacks.
When not trying to be a Network Security Magician, he visits Historical European ruins with his family.
Mareike is a Channel Sales Engineer at Delinea, driving channel strategy and partner enablement for Delinea's portfolio of products. She is based in Pforzheim, Germany, and joined Delinea 2 years ago directly after her studies.
Mareike has worked with dozens of customers in the DACH region over the past years and has delivered several webinars. With her experience, she is currently focusing on Delinea's channel partners, helping them and their customers use Delinea's PAM solution to mitigate the ever-growing security risks and meet security requirements such as the recently released EU NIS2 directive.
In her spare time, she is trying to become the next Picasso of the international art world.

Tomislav Lukačević
Consultant
at Hewlett Packard Enterprise
Introduction to Security Service Edge (SSE). Start by eliminating your VPN | .tech
Emergence of hybrid workplace enabled employees to work from anywhere. At the same time, IT services became hybrid, a blend of on-premises, hosted in public cloud and SaaS. Learn what is Security Service Edge and how it addresses challenges of hybrid workforce and hybrid IT deployment models. Get familiar with terms like ZTNA, SWG and CASB and how can you make first step in SSE by eliminating VPN.
Tomislav is an IT professional with more than 15 years of experience in technology consulting. He worked with many customers in Croatia, helping them plan and design their IT infrastructure. After initial focus on servers, storage and virtualization, Tomislav has shifted his focus on networking and security, helping customers design their network environments with security as integral part of the network. Tomislav holds a Master’s degree in Telecommunications at the Faculty of Electrical Engineering and Computing, University of Zagreb.

Tomislav Poljak
Cyber Security Consultant
at Microsoft Croatia
Identity management from a secure workstation - challenges and alternatives | .ops
Managing identities and assigned privileges for users with elevated administrative IT rights (IT admins, database and application admins, Security operations) is a critical security measure that every company should incorporate into its environment. Privileged users need to be monitored and scrutinized for their actions and behaviors both on their workstations machines and in the cloud systems. Beyond the technical challenges of securely administering IT systems, operational issues often arise for companies only after the implementation of a specific solution.
In this presentation, through demonstrations and practical examples, Tomislav will illustrate how to prepare an organization for the implementation of a secure workstation or other Privileged Access Management (PAM) solutions. He will delve into methods for controlling and tracking activities of privileged users, as well as the authentication and authorization mechanisms that need to be monitored using supervisory tools. Join him to explore the realm where security meets administration, and gain insights into establishing a robust defense against potential breaches while ensuring operational integrity.
Tomislav works at Microsoft Croatia (for the past eleven years) as a cyber security consultant. He’s mostly involved in the recovery of enterprise systems after cyber attacks, but also at a time without reactive engagements, he helps customers to establish SOC environments and carries out various jobs like monitoring, protection, and prevention to increase their security. Lately, there has been an increasing number of cyber attacks, so he’s focusing on enhanced education, preventive engagements, and assessments that determine the state of the identity system.
He often speaks at conferences in Croatia and the near region. He’s Microsoft certified trainer (MCT) since 2008 and hold other industry certificates. Whenever possible he spends time in nature, in any leisure or work activities.

Tomislav Vuk
Cybersecurity consultant
at DRC-Servis
Preparing for Evolving Threats: AI agentic attacks, Deepfake maturation and Polymorphing phishing | .ops
AI is evolving and becoming more available to everyone. Statistics show rise of AI tools in cyber attacks, in social engineering but also development of agentic AI attacks. Autonomous AI-driven threats are capable of strategizing, pivoting, and executing multi-stage campaigns with minimal or no human input. Hyper-realistic deepfake media moving beyond novelty into weaponized disinformation, social engineering, and fraud. Next-gen phishing re-shape content, language, and delivery channels to bypass filters and exploit human trust at scale. Are we falling short and what can we do about it?
Tomislav is an engineer and entrepreneur who’s spent years in cyber security. He is a frequent speaker on cyber risks, and focuses on helping others understand cyber threats before they strike, combining technical expertise with entrepreneurial insight to make cybersecurity less abstract to the audience and raise awareness on all levels.

Transparency, Compliance and Reaction on Attacks
at Demo sessions
Transparency, Compliance and Reaction on Attacks
A workshop/demo session by Enginsight, divided into three segments - you can book each one separately.
14.00 - 14.20: Transparency: Know Your IT Weaknesses Before the Hacker Does
Duration: 20–25 minutes
Description:
In today’s rapidly evolving threat landscape, visibility is key. This session will explore how you can gain comprehensive transparency across your IT environment, helping you identify vulnerabilities and weak points before attackers do. Attendees will learn how to continuously monitor systems, discover misconfigurations, and detect risky access points. We’ll demonstrate how this platform provides actionable insights, enabling IT teams to prioritize remediation and strengthen their security posture proactively rather than reactively.
Key Takeaways:
• Real-time visibility into your network and assets
• Identifying hidden vulnerabilities and configuration gaps
• Prioritizing risks with actionable intelligence
• How to make transparency an ongoing, automated process
-
Register for this session here.
14.30 - 14.50: Compliance: What About NIS2 and ISO?
Duration: 20–25 minutes
Description:
Regulations like NIS2 and standards like ISO 27001 demand that organizations maintain strict compliance across all IT systems. This session will cover how you can simplifiy compliance management by automating audits, tracking controls, and providing clear reporting. Learn how the platform maps your IT environment against regulatory requirements, highlights gaps, and provides actionable recommendations for achieving and maintaining compliance. Perfect for IT teams that want to reduce manual effort and ensure readiness for any inspection.
Key Takeaways:
• Understanding NIS2 and ISO 27001 requirements
• Mapping IT systems and processes to compliance standards
• Automated evidence collection and reporting
• How to maintain compliance continuously
-
Register for this session here.
15.00 - 15:20 Reaction on Attacks: What IDS/IPS Really Means to a Contemporary IT-Sec Level
Duration: 20–25 minutes
Description:
Detection and response are critical in today’s threat landscape. This session dives into the role of IDS/IPS (Intrusion Detection and Prevention Systems) in a modern security strategy. We’ll explore how attacks are detected, prioritized, and responded to efficiently. Attendees will see how the platform correlates events across systems, alerts teams to suspicious behavior, and helps orchestrate timely responses. Learn what effective reaction looks like in a contemporary IT environment and how can you stay ahead of threats.
Key Takeaways:
• Understanding IDS/IPS in the context of modern threats
• Real-time alerting and event correlation
• Prioritizing incidents and reducing response times
• How to automate and streamline attack response
-
Register for this session here.

Vanja Švajcer
Technical Leader
at Cisco Talos
The growth of commercial spyware based intelligence providers without legal or ethical supervision | .ops
Attackers have long used commercial products developed by legitimate companies to compromise targeted devices. These products are known as commercial spyware. Commercial spyware operations mainly target mobile platforms with zero- or one-click zero-day exploits to deliver spyware. This threat initially came to light with the leaks of HackingTeam back in 2015, but gained new notoriety with public reporting on the NSO Group, and, in the years that have followed, the landscape has exploded.
Commercial spyware has become so notorious that international governments are taking notice and action against it, as evidenced by the Biden administration’s recent Executive Order on commercial spyware. A recent report from the United Kingdom’s National CyberSecurity Center (NCSC) highlights the accessibility of these tools “lowers the barrier to entry to state and non-state actors in obtaining capability and intelligence.” As recently as June 2023, the European Parliament’s plenary session voted on an ongoing investigation concerning the illicit usage of NSO’s Pegasus and equivalent surveillance spyware by EU member states (PEGA report).
However, limited legal and legislative actions are yet to have an immediate positive effect on curbing the use of commercial spyware. Despite these steps toward limiting the operations of these spyware companies, they are likely to keep operating in any region as long as it's financially and legally feasible. Increasing scrutiny with export regulations, criminal liability and fines may be a way forward towards ensuring that their activity does not go beyond the legitimate purposes they advertise. We dig into technical and ethical details of commercial spyware threats.
Vanja Svajcer works as a Technical Leader at Cisco Talos. He is a security researcher with more than 20 years of experience in malware research, cyber threat intelligence and detection development. Vanja enjoys tinkering with automated analysis systems, reversing binaries and analysing mobile malware. He thinks all the time spent hunting in telemetry data to find new attacks is well worth the effort. He presented his work at conferences such as Virus Bulletin, RSA, CARO, AVAR, BalCCon and others.

Vanja Švajcer
Threat Researcher
at Cisco Talos
Contagious Interview - Beavertail, OtterCookie and InvisibleFerret | .tech
Attack groups linked to activities aligned with North Korean state interests, whose main goal is financial gain, often achieve their objectives through the theft of digital currencies or direct influence on electronic payment protocols (e.g., SWIFT), thereby contributing to the North Korean budget, which otherwise struggles to be filled with foreign currencies due to numerous sanctions.
One technique used by financially oriented groups is the creation of fake employees and fake recruitment agents to assume the identities of real software engineers and secure employment through compromised user credentials. Perhaps the most well-known operation of this type is the Contagious Interview campaign, first recorded at the end of 2023, but still active today.
The Contagious Interview campaign is intriguing because it targets actual engineers as well as enterprise recruiters. The attack employs a series of notable techniques, which we cover in this session. We will demonstrate how attackers approach victims, what tools they use, and their objectives. The presentation is the result of research and monitoring of the activities of the group known as Famous Chollima by Palo Alto Unit 42 and Wagemole by ESET.
Vanja Švajcer works as a Threat Researcher at Cisco Talos. Vanja enjoys tinkering with automated analysis systems, reversing binaries and analysing mobile malware. He thinks time spent scraping telemetry data to find indicators of new attacks is well worth the effort. He presented his work at conferences such as FSec, Bsides, Virus Bulletin, RSA, CARO, AVAR, BalcCon and others.

Vanja Švajcer
Technical Leader
at Cisco Talos
Exploring malicious Windows drivers | .tech
Drivers have long been of interest to threat actors, whether they are exploiting vulnerable drivers or creating malicious ones. Malicious drivers are difficult to detect and successfully leveraging one can give an attacker full access to a system.
With the existence of malicious drivers, there is a need for those who can analyze identified samples. This analysis requires specific knowledge of the Windows operating system, which can be difficult to acquire. Windows drivers and the kernel can be overwhelming to learn about, as these topics are vast and highly complex. The documentation available on these subjects is daunting and difficult to navigate for newcomers, even for those with programming experience.
This initial hurdle and steep learning curve create a high barrier of entry into the subject. To many, the kernel space seems to be an arcane and hidden part of the operating system.
This presentation will be a high-level introduction into drivers, their usage by malicious actors and the Windows kernel. No previous experience of drivers is required.
Vanja Švajcer works as a Technical Leader at Cisco Talos. He is a security researcher with more than 20 years of experience in malware research, cyber threat intelligence and detection development. Vanja enjoys tinkering with automated analysis systems, reversing binaries and analysing mobile malware. He thinks all the time spent hunting in telemetry data to find new attacks is well worth the effort. He presented his work at conferences such as Virus Bulletin, RSA, CARO, AVAR, BalCCon and others.

Vladimir Ožura
Cybersecurity Consultant
at Microsoft Croatia
Common Challenges in Cyber Incident Response Engagements | .tech
Cyber incident response is a critical process that aims to minimize the impact of cyberattacks and restore normal operations as quickly as possible. However, cyber incident response engagements often face various challenges from both the customer side and the vendor side. These challenges can affect the effectiveness and efficiency of incident response, as well as the trust and collaboration between the customer and the vendor. In this presentation, Vladimir will discuss some of the most common challenges and questions asked by customers during cyber incident response engagements. Vladimir will also share some of the best practices and lessons learned from experience in providing cyber incident response support to various customers across different industries and regions. This presentation will help you understand the challenges and opportunities in cyber incident response, and how to improve your readiness and resilience against cyberattacks.
Vladimir has over 10 years of experience in the cyber security space and currently works at Microsoft Croatia (for the past 2 years) as a cyber security consultant. He's mostly involved in leading cyber security incident response engagements on a global scale and diving deep into data analysis to uncover the attack story. Part of his role as a lead investigator is not only providing investigation findings, but also recommendations to increase the security posture of environments. He is also a trainer for Threat Hunting and a member of the Delivery Excellence team. Vladimir holds several industry leading certificates including GCFE, GCDA and GSOM. Whenever possible he spends time hiking and hanging out with the family.

Wojciech Regula
Principal Security Specialist
at SecuRing
macOS Red Teaming in 2023 | .tech
Do you have Macs in your company's infrastructure? Nowadays, I bet that in most cases the answer would be YES. Macs stopped be computers only used in startups. We can observe them even in huge legacy environments in banks and other corporations. The problem is that they are usually not symmetrically secured, comparing to the rest of Windows stations. Macs are not immune, they can be insecurely configured and now... even Apple admits that malware is present on Macs.
In this presentation I will:
* Introduce you to macOS security mechanisms
* Perform step by step macOS infection basing on my 0-day (live demo)
* Show you post exploitation techniques
* Attack installed apps and collect data from them
* Give recommendations on how to harden your Mac and macOS infrastructure
Wojciech is a Principal Security Specialist working at SecuRing. He specializes in application security on Apple devices. He created the iOS Security Suite - an opensource anti-tampering framework. Bugcrowd MVP, found vulnerabilities in Apple, Facebook, Malwarebytes, Slack, Atlassian, and others. In free time he runs an infosec blog - https://wojciechregula.blog. Shared research on among others Black Hat (Las Vegas, USA), DEF CON (Las Vegas, USA), Objective by the Sea (Hawaii, USA), AppSec Global (Tel Aviv, Israel), TyphoonCon (Seoul, South Korea), NULLCON (Goa, India), CONFidence (Cracow, Poland).

Zlatan Stilinović
Lead coordinator, Microsoft Security
at Privredna Banka Zagreb
Juggling with Silver Bullets | .lead
Complex organizations require complex cybersecurity solutions, and every administrator's wish is that their maintenance does not become a nightmare. In this interactive lecture, we will demonstrate, using the example of an imaginary complex company that has various security solutions implemented in its system, how this could or should look. Can these solutions work together and bring synergy, or do they generate additional noise in the communication channel? Introducing a new solution that controls previously uncovered blind spots in such a system can be a demanding task, and the question often arises whether its contribution justifies the overall improvement of the company. Through the presentation, we will also show several cases where information about a problem that may not be visible to the "naked eye" can be obtained from different sources. And when the problem is known, its solution is not far away.
At a crossroads in my life, when hosting between becoming a chef or pursuing something related to my studies in electrical engineering, I chose the second one. Now, I cook for personal enjoyment, and I earn a living by administering IT systems with a focus on security solutions. I look forward to the new challenges that hackers present to us every day.
My bicycle patiently endures our joint commutes to work because it knows that, as soon as the opportunity arises, it will end up on some road, hill, and/or terrain.

Zoran Cetinjanin
ICT technology advisor
at City of Karlovac
Challenges of implementing the NIS2 Directive in cities | .ops
Most cities are required to implement the NIS2 Directive. The digital transformation of cities introduces numerous new services, introduces video surveillance and IoT devices, which increase the vulnerability of the system and access to sensitive citizen data. Education and awareness of cyber threats are at a low level, and the fragmentation of IT systems and lack of understanding of the administration create an environment with financial constraints. In this lecture, using the example of the City of Karlovac, we will show how to successfully deal with these challenges in order to ensure a secure and reliable critical infrastructure.
Zoran has been working in the City of Karlovac for more than 20 years as an ICT technology advisor, where he continuously introduces new solutions while respecting the principles of ensuring cybersecurity and system reliability. In his work, he has encountered various cyberattacks. He is also the president of the ICT Working Group in the Association of Cities, which brings together 127 cities in Croatia, bringing together ICT experts from these cities for the purpose of exchanging experiences and finding optimal solutions for everyone.
In his free time, if he has any, he spends his energy charging and discharging it by hiking, cycling, and hitting a tennis ball.
Falkensteiner Punta Skala, hotel IADERA
Punta Skala bb, HR-23231 Petrčane
Email
[email protected]

Falkensteiner Hotel & Spa Iadera at Punta Skala Resort
the best suited mid-Dalmatian conference venue waits for the participants of DEEP

Venue
Looking for starting in very best possible manner, DEEP proudly presents an excellent venue for the conference, to be held from 21st to 22nd of October 2026. We are proud to welcome you to glorious five-star Falkensteiner Hotel & Spa Iadera
Hotel & Spa Iadera - part of famous Falkensteiner Punta Skala Resort, one of most respected tourist complexes in whole Adriatic area. Resort is conveniently situated just a short drive from vibrant city of Zadar but it also contains all the facilities any conference attendee might need during a stay. We have a huge experience in organizing similar events, and it assured us that single-point conference is the most convenient way for our guests and visitors to enjoy both the conference and any free time dedicated to themselves.

Apart from breath-taking location directly at the top of the Peninsula and exclusive 5-star service, at our chosen venue you can also enjoy Mediterranean cuisine with hotel restaurant, fish restaurant Bracera, Steak house Planika and Hideout beach bar directly at the sea.
Should you want to stay for the weekend, there are several great areas for visiting, from the ancient town of Zadar, famous - among other things - for the most beautiful sunset in the world, to the national parks of Velebit and Kornati or worldwide known sci-fi landscapes of island Pag.

We are looking forward to be your hosts at this magnificent hotel during the conference. Online registrations will start soon, offering you accommodation in single or double rooms at this hotel during the process, at special prices agreed with Falkensteiner Hotels & Residences, available only to the DEEP attendees. Should you have any additional questions please be free to ask us at [email protected]. We are sure that this venue will fully enhance your experience and make your stay there during DEEP more enjoyable.
Terms and Conditions
Privacy Statement
We are obliged to protect our customer's personal data by collecting only the necessary information required to meet our obligations. Customer identification data that is considered personal consists of: name and surname, e-mail address and phone number, or data that are not publicly available. All customer information is strictly kept and is only available to employees who are required to perform this job. All our employees and business partners are responsible for respecting the privacy principles. Your personal information will be kept confidential and will not be distributed, disclosed, made available to third parties or otherwise made available to any third party without your prior consent.
Order of payments
At the time the order is received, Avola Solutions d.o.o. will inform the buyer electronically that the purchase has been successfully completed. The purchase contract is concluded after a successful payment by debit and / or credit cards or upon receipt of a bank transfer.
Payment of ordered items can be done by cards: Visa, Maestro, Diners, American Express, MasterCard or bank transfer.
Payment Security
The deep-conference.com website is committed to providing personal data protection, by collecting only essential, basic customer information. All customer information is strictly kept and only accessible to employees who are required to do this. All employees of Avola Solutions d.o.o. and business partners are responsible for adhering to the privacy principles.
The secrecy of your data is protected and secured by using SSL encryption. Web payment pages are secured using Secure Socket Layer (SSL) protocols with 128-bit data encryption. SSL Encryption is a data encryption process to prevent unauthorized access when transmitted.
This ensures secure data transfer and disables unauthorized access to data when communicating between the user's computer and payment service, and vice versa.
The payment service used is certified according to the PCI DSS Level 1 security standard prescribed by Visa and MasterCard.
The merchant does not store credit card numbers and numbers are not available to unauthorized persons.
The payment service is based on the 3-D Secure standard that currently offers the safest payment solution for credit and debit cards in the internet environment.
If the user card is part of the 3-D Secure program, the customer will be asked for an additional identity check as a confirmation that he is using the card.
Delivery and Disputes
Order confirmations and other information are delivered to the customer by e-mail to the address registered on the user's profile. Avola Solutions is not responsible for the damage caused by the misspelling of the email address in the user profile or because of the inability to deliver confirmation and other information caused by technical issues on the part of the e-mail service provider.
The customer will receive an invoice electronically.
Reservation without a purchase is not possible. Refunds for purchased goods are also not possible.
Any additional questions as well as any complaints about the lack of service and all other objections can be made in writing through electronic or regular mail:
to e-mail address: [email protected]
to the address: Kuniščak 1B, 10000 Zagreb, Republic of Croatia
In case of dispute about the justification of the complaint and if the Buyer, on the basis of a subjective assessment, finds that he has not received adequate service, it is customary in the business practice to report the case to one of the competent institutions. The competent and official bodies then make all necessary checks to ascertain the correctness and respect of the applicable laws. The court in Zagreb is competent for all possible disputes.
Terms of Use
The buyer is obligated to familiarize himself with these Terms and Conditions before making a purchase and to check them upon each visit of this web site in order to be familiar with all rights and obligations. If buyer does contrary, the Seller is considered free of any liability.
Reservation without a purchase is not possible. The currency of payment is Euro (EUR). The service prices are expressed with VAT.
It is considered that the purchase agreement was concluded after a successful Payment Transaction with Visa, Maestro, Diners, American Express or MasterCard cards or after the receipt of a bank payment.
About Us
Full company name
Avola Solutions d.o.o.
Registered number
040188508
VAT number
78288303547
Company address
Kuniščak 1B, 10000 Zagreb, Croatia
Contact phone and e-mail
Phone: +385 1 333 6216
E-mail: [email protected]
More details can be found here.
Uvjeti korištenja
Izjava o privatnosti
Obavezujemo se štititi osobne podatke naših kupaca, na način da prikupljamo samo nužne podatke koji su potrebni za ispunjenje naših obveza. Pod osobnim podacima smatraju se identifikacijski podaci kupca: ime i prezime, e-mail adresa i broj telefona, odnosno podaci koji inače nisu javno dostupni. Svi se podaci o kupcima strogo čuvaju i dostupni su samo djelatnicima kojima su ti podaci nužni za obavljanje posla. Svi naši djelatnici i poslovni partneri odgovorni su za poštivanje načela zaštite privatnosti. Vaše osobne podatke čuvaju se u tajnosti, te ih se neće distribuirati, objavljivati, davati trećim stranama na korištenje niti ih na bilo koji drugi način učiniti dostupnima bilo kojoj trećoj osobi bez vaše prethodne suglasnosti.
Narudžbe i način plaćanja
U trenutku kada narudžba bude zaprimljena, Avola Solutions d.o.o. će elektroničkim putem u obliku e-pošte obavijestiti Kupca o tome da je kupnja uspješno izvršena. Ugovor o kupnji je sklopljen nakon uspješno obavljenog plaćanja debitnim i/ili kreditnim karticama ili po primitku bankovnog transfera.
Plaćanje naručenih stavki moguće je obaviti karticama: Visa, Maestro, Diners, American Express i MasterCard ili bankovnim transferom.
Sigurnost plaćanja
Web stranica deep-conference.com obavezuje se pružati zaštitu osobnim podacima kupaca, na način da prikuplja samo nužne, osnovne podatke o kupcima. Svi se podaci o korisnicima strogo čuvaju i dostupni su samo djelatnicima kojima su ti podaci nužni za obavljanje posla. Svi djelatnici Avola Solutions d.o.o. i poslovni partneri odgovorni su za poštivanje načela zaštite privatnosti.
Tajnost Vaših podataka je zaštićena i osigurana uporabom SSL enkripcije. Stranice za naplatu putem interneta osigurane su korištenjem Secure Socket Layer (SSL) protokola sa 128-bitnom enkripcijom podataka. SSL enkripcija je postupak šifriranja podataka radi sprječavanja neovlaštenog pristupa prilikom njihovog prijenosa.
Time je omogućen siguran prijenos informacija te onemogućen nedozvoljen pristup podacima prilikom komunikaciji između korisnikovog računala i servisa plaćanja, te obratno.
Korišteni servis plaćanja je certificiran prema PCI DSS Level 1 sigurnosnom standardu propisanom Visa i MasterCard pravilima.
Trgovac ne pohranjuje brojeve kreditnih kartica i brojevi nisu dostupni neovlaštenim osobama.
Servis plaćanja je temeljen na 3-D Secure standardu koji trenutno nudi najsigurnije rješenje plaćanja kreditnim i debitnim karticama u internet okruženju.
Ukoliko kartica korisnika sudjeluje u 3-D Secure programu od kupca će se tražiti dodatna provjera identiteta kao potvrda da upravo on koristi karticu.
Dostava i reklamacije
Potvrde i ostali podaci se dostavljaju kupcu putem e-maila na adresu koja je upisana na profilu korisnika. Avola Solutions ne odgovara za štetu nastalu krivim upisivanjem e-mail adrese u korisničkom profilu ili zbog nemogućnosti isporuke potvrda i ostalih informacija uzrokovane tehničkim problemima sa strane davatelja e-mail usluge.
Kupac će elektroničkim putem dobiti i račun.
Rezervacija bez kupnje nije moguća. Povrat naknade za kupljena dobra također nije moguć.
Sva dodatna pitanja kao i eventualne reklamacije u svezi nedostatka usluge te svi ostali prigovori mogu se izjaviti u pisanoj formi putem elektroničke ili obične pošte:
na e-mail adresu: [email protected]
na adresu: Kuniščak 1B, 10000 Zagreb, Republika Hrvatska
U slučaju spora oko opravdanosti reklamacije te ukoliko Kupac temeljem subjektivne procjene smatra da nije dobio adekvatnu uslugu, u poslovnoj praksi je uobičajeno da se slučaj prijavi jednoj od nadležnih institucija. Mjerodavna i službena tijela tada vrše sve potrebne provjere radi utvrđivanja ispravnosti te poštivanja važećih zakona. Za sve eventualne sporove nadležan je sud u Zagrebu.
Uvjeti korištenja
Kupac je dužan prije kupnje upoznati se sa ovim Uvjetima te iste provjeravati prilikom svake posjete predmetne Internet stranice, kako bi bio upoznat sa svim pravima i obvezama. Suprotno postupanje oslobađa Prodavatelja bilo kakve odgovornosti.
Isporučitelj (Prodavatelj) je Avola Solutions d.o.o. Kupac robe je posjetitelj web shopa koji odabere neku od ponuđenih usluga i plati je kreditnom ili debitnom karticom ili bankovnim transferom.
Rezervacija usluga bez kupnje nije moguća. Valuta plaćanja je Euro (EUR). Cijene usluga su iskazane s PDV-om.
Smatra se da je ugovor o kupnji sklopljen nakon uspješno obavljene transakcije plaćanja putem Payment Gateway-a s Visa, Maestro, Diners, American Express i MasterCard karticama ili nakon zaprimljene bankovne uplate.
O nama
Puni naziv tvrtke
Avola Solutions d.o.o.
MBS
040188508
OIB tvrtke
78288303547
Adresa sjedišta tvrtke
Kuniščak 1B, 10000 Zagreb, Republika Hrvatska
Kontakt telefon i e-mail
Tel: +385 (0)1 333 6216
E-mail: [email protected]
Više detalja možete pronaći ovdje.